#OSINT Tool Tuesday
It’s the third week of the year and time for another set of tools to help you with your work in OSINT. This week will be:
[+] Spaghetti Bookmarklet (mine)
[+] Tab management/automation
[+] OnlyFans?
RT for Reach!
🙏
👇(1/5)
It’s the third week of the year and time for another set of tools to help you with your work in OSINT. This week will be:
[+] Spaghetti Bookmarklet (mine)
[+] Tab management/automation
[+] OnlyFans?
RT for Reach!
🙏
👇(1/5)

The first #OSINT tool is a bookmarklet I built called Forage and is meant to expand your search across popular social media sites. It takes the username from FB/IG, Twitter, and LinkedIn and expands your search across the web. Expect updates!
github.com/jakecreps/fora…
☝️👇(2/5)
github.com/jakecreps/fora…
☝️👇(2/5)
The second #OSINT tool is a browser extension called TabTrum that takes a snapshot of your active tabs and saves them so you can reopen that same combination again with one click. It's saved me SO much time with work and OSINT investigations.
tabtrum.live
☝️👇(3/5)
tabtrum.live
☝️👇(3/5)
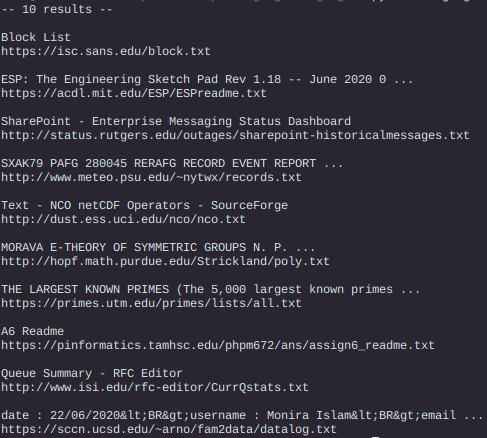
The third #OSINT tool is a search engine for OnlyFans. Use responsibly. If you're working on a catfish case, investigating benefits fraud, etc. it can be very useful. The index isn't great, but it's a decent starting point.
onlysearch.co
☝️👇(4/5)
onlysearch.co
☝️👇(4/5)
Remember #OSINT != tools. Tools help you plan and collect data, but the end result of that tool is not OSINT. You have to analyze, receive feedback, refine, and produce a final, actionable product of value before you can call it intelligence.
Thanks for reading!
☝️(5/5)
Thanks for reading!
☝️(5/5)
• • •
Missing some Tweet in this thread? You can try to
force a refresh