A May 3rd 2021 tweet from @SpokespersonCHN about a boy with serious arm injuries being flown to Xinjiang for medical treatment attracted a flurry of retweets and repetitive replies in multiple languages from accounts with default profile pics.
cc: @ZellaQuixote
cc: @ZellaQuixote

These replies are from a network of 479 accounts created in batches between January and April 2021. All accounts have English first and last names (first names are almost all female). These accounts have thus far posted all of their tweets via the Twitter Web App (allegedly). 





This network's content is (mostly) a mix of replies and retweets. The replies are repeated verbatim across multiple accounts. Despite all of the accounts having English-looking names, the accounts are quite multilingual, having replied in 37 different languages thus far. 


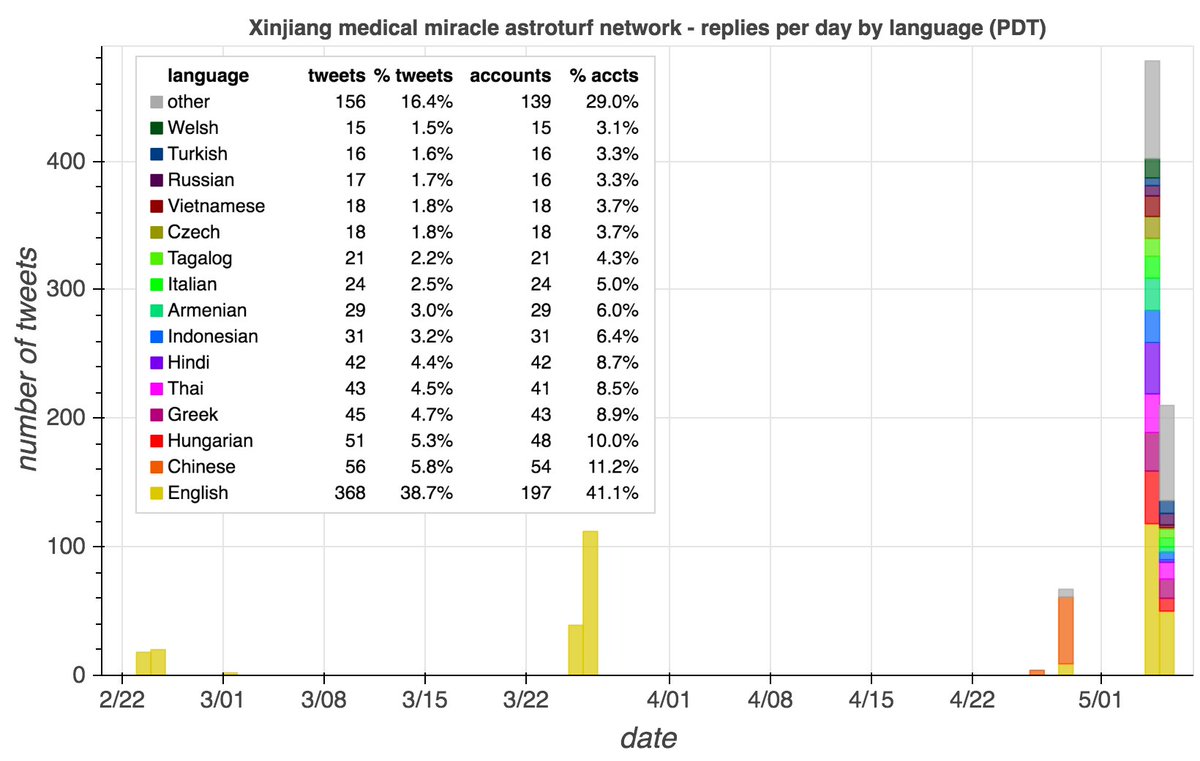
The bulk of this network's amplification thus far is of two recent tweets about the injured boy's surgery in Xinjiang, which were retweeted and replied to by hundreds of members of the network. Previously, part of the network boosted tweets about COVID conspiracist Li-Meng Yan. 

• • •
Missing some Tweet in this thread? You can try to
force a refresh