BREAKING: Biden signs sweeping cyber EO to close gaps exposed by SolarWinds.
Highlights:
* Incident reporting reqs for IT contractors
* Security reqs for software contractors
* Encryption, MFA, EDR reqs for agencies
* Cyber incident review board
Story: subscriber.politicopro.com/article/2021/0…
Highlights:
* Incident reporting reqs for IT contractors
* Security reqs for software contractors
* Encryption, MFA, EDR reqs for agencies
* Cyber incident review board
Story: subscriber.politicopro.com/article/2021/0…
More highlights:
* Pushes toward zero-trust architecture
* FedRAMP cloud security modernization
* New fed cloud strategy
IoT security labeling pilot program
* Encourages SBOM
* CISA incident response "playbooks" for agencies
* Govt-wide log retention/analysis policy
* Pushes toward zero-trust architecture
* FedRAMP cloud security modernization
* New fed cloud strategy
IoT security labeling pilot program
* Encourages SBOM
* CISA incident response "playbooks" for agencies
* Govt-wide log retention/analysis policy
The EO "makes a down-payment towards modernizing our cyber defenses" and "reflects a fundamental shift in our mindset from incident response to prevention, from talking about security to doing security," a sr admin official told reporters.
“For too long, we fail to take the necessary steps to modernize our cybersecurity defenses, because doing so takes time, effort, and money, and instead we've accepted that we’ll move from one incident response to the next," SAO said.
“We routinely install software with significant vulnerabilities into some of our most critical systems and infrastructure," SAO added. "The cost of the continuing status quo is simply unacceptable.”
The SAO offered a compelling analogy: “We’d never buy a family minivan knowing it could have potentially fatal defects, with the expectation of recalls or [deciding] whether you want to install and pay for seatbelts or airbags afterwards.”
Here is the text of Biden's cyber EO: whitehouse.gov/briefing-room/…
Fact sheet: whitehouse.gov/briefing-room/…
My story: politico.com/news/2021/05/1…
Fact sheet: whitehouse.gov/briefing-room/…
My story: politico.com/news/2021/05/1…
Let's dive into Biden's cyber EO, shall we?
Here's a look at the key provisions...
Here's a look at the key provisions...
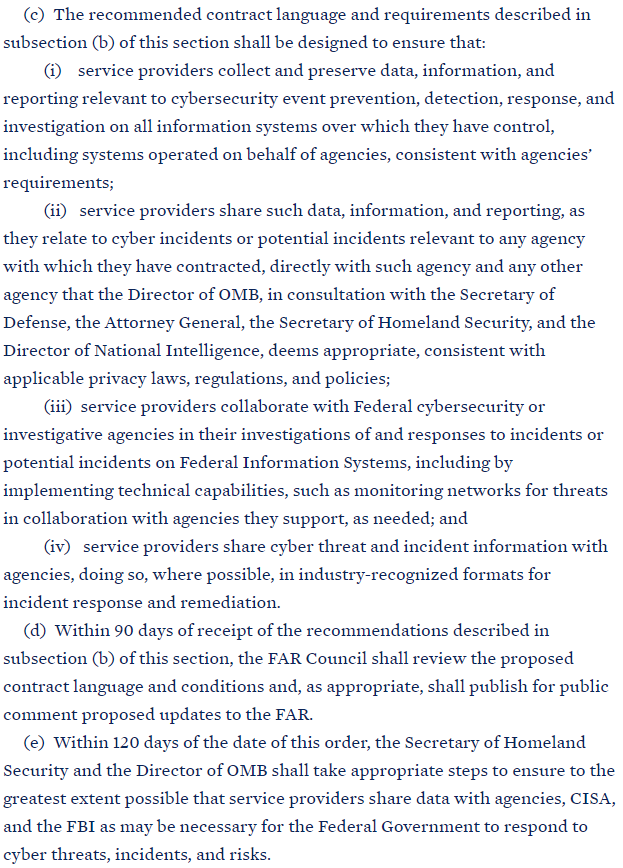
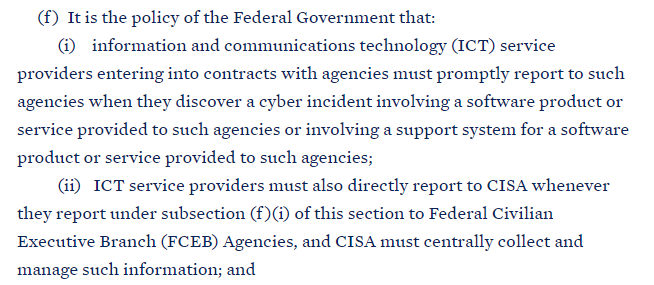
OMB must recommend to federal acquisition officials a major overhaul of contracting language with new cybersecurity requirements for IT service providers that contract with the government.
CISA must recommend standardized cyber contract language for universal use.



CISA must recommend standardized cyber contract language for universal use.
Requirements for agencies:
* Plans for cloud adoption and zero-trust architecture
* Encryption and MFA within 180 days
* New OMB/CISA cloud security strategies and guidance
* FedRAMP (cloud service marketplace) modernization



* Plans for cloud adoption and zero-trust architecture
* Encryption and MFA within 180 days
* New OMB/CISA cloud security strategies and guidance
* FedRAMP (cloud service marketplace) modernization
Software security stuff:
* NIST must develop software security guidance
* Commerce must publish minimum reqs for software bill of materials (think ingredient list for software)
* Defining, identifying, and protecting most critical software
* Ensuring vendor security compliance



* NIST must develop software security guidance
* Commerce must publish minimum reqs for software bill of materials (think ingredient list for software)
* Defining, identifying, and protecting most critical software
* Ensuring vendor security compliance
* IoT security labeling pilot program (think Energy Star)
* Cyber Safety Review Board: composition (co-led by DHS and industry rep, includes DOD, DOJ, CISA, NSA, FBI), function (think NTSB), and initial reporting requirement (SolarWinds review)



* Cyber Safety Review Board: composition (co-led by DHS and industry rep, includes DOD, DOJ, CISA, NSA, FBI), function (think NTSB), and initial reporting requirement (SolarWinds review)
* CISA must create incident response playbooks so all agencies are responding in a consistent way
* Civilian agencies must use EDR software to aid in threat detection
* DOD/IC must improve detection on natsec systems
* CISA must report on use of its new threat hunting authority



* Civilian agencies must use EDR software to aid in threat detection
* DOD/IC must improve detection on natsec systems
* CISA must report on use of its new threat hunting authority
* DHS & DOD must share w/ each other their network security directives and consider whether to adopt each other's requirements
* DHS must recommend a log retention policy and OMB must review and issue it
* DOD/IC must adopt standards at or above what's in this EO


* DHS must recommend a log retention policy and OMB must review and issue it
* DOD/IC must adopt standards at or above what's in this EO
That's what I flagged on my review. Did I miss any particularly juicy sections? Let me know!
Some praise from industry groups — many of whose members will have to comply with the new security regulations — for Biden's cyber EO. 


Leading cyber-focused lawmakers also praised Biden's EO, although several of them noted that it will not be enough and Congress has to act, too. 


• • •
Missing some Tweet in this thread? You can try to
force a refresh