Over $600 million reportedly stolen in cryptocurrency hack - @Ax_Sharma
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
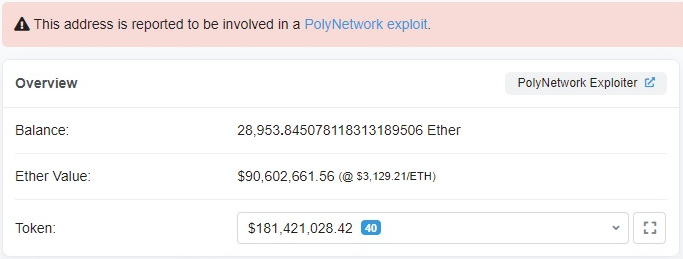
@Ax_Sharma Attack on Poly Network ended with the hacker transferring Binance Chain, Ethereum, and Polygon assets to three wallets they control:
Ethereum tokens: $273 million
Binance Smart Chain: $253 million
Polygon Network (in USDC): $85 million
Ethereum tokens: $273 million
Binance Smart Chain: $253 million
Polygon Network (in USDC): $85 million
@Ax_Sharma The hacker's three wallets have been reported to exchanges to prevent the attacker from converting the assets and splitting with the money. 
@Ax_Sharma There are some traces regarding the identity of the hacker but nothing has been confirmed yet.
In the meantime, the attacker has been receiving transactions with messages and tips on how to launder the $$ and the actions against them.
In the meantime, the attacker has been receiving transactions with messages and tips on how to launder the $$ and the actions against them.
@Ax_Sharma The hacker rewarded one tipster with ETH 13.37 (leet), currently ~ $40k, for warning them of tokens being blacklisted.
• • •
Missing some Tweet in this thread? You can try to
force a refresh