Hackers now backdoor Microsoft Exchange using ProxyShell exploits - @LawrenceAbrams
bleepingcomputer.com/news/microsoft…
bleepingcomputer.com/news/microsoft…
We knew exploits would be coming when we reported about active ProxyShell scans last week.
bleepingcomputer.com/news/microsoft…
bleepingcomputer.com/news/microsoft…
Well it's begun today - threat actors are now actively exploiting Microsoft Exchange server with the ProxyShell vulnerability to drop webshells and backdoors.
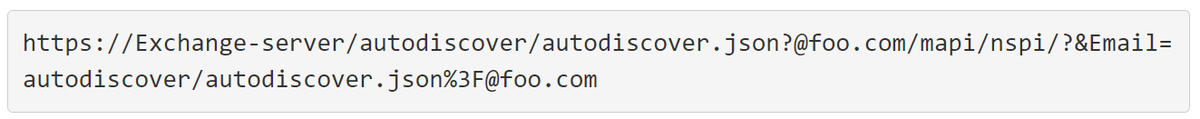
First spotted by @GossiTheDog, @buffaloverflow, and @bad_packets, threat actors are chaining together vulnerabilities discovered by @orange_8361 (CVE-2021-34473, CVE-2021-34523, and CVE-2021-31207) in an RCE attack known as ProxyShell.
https://twitter.com/buffaloverflow/status/1425831100157349890
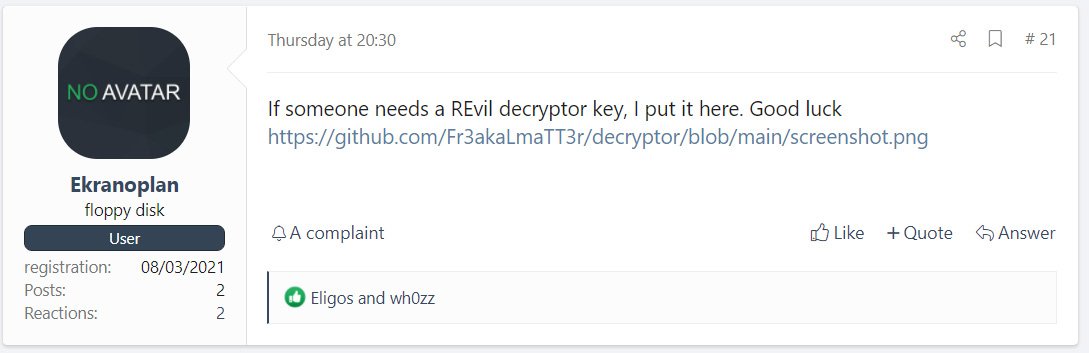
Initial scans for vulnerable devices are targeting Microsoft Exchange's AutoDiscover service.
Note: the email address does not need to be valid and change between threat actors.
Note: the email address does not need to be valid and change between threat actors.
The attacks are currently dropping webshells that are being used by threat actors to upload various executables and other webshells.
@buffaloverflow told us that one attack is creating a scheduled task that launches a .NET backdoor that is currently pulling down a benign payload
@buffaloverflow told us that one attack is creating a scheduled task that launches a .NET backdoor that is currently pulling down a benign payload
For those familiar with March's ProxyLogon attacks, the webshells look similar (but not exactly the same) to the China Chopper shells used in that campaign.
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
As more servers are compromised, it is expected that the threat actors will replace the current payload with a malicious one.
Bad Packets (@bad_packets) said that they have seen scans from 3.15.221.32 and 194.147.142.0/24 located in the USA, Iran, and the Netherlands. 
To check if your Exchange server is being scanned for ProxyShell, you can use this Azure Sentinel query shared by @GossiTheDog.
W3CIISLog
| where csUriStem == "/autodiscover/autodiscover.json"
| where csUriQuery has "PowerShell" | where csMethod == "POST"
W3CIISLog
| where csUriStem == "/autodiscover/autodiscover.json"
| where csUriQuery has "PowerShell" | where csMethod == "POST"
If you manage an Exchange server and have not installed April cumulative updates or later, get to it or you will likely be targeted.
Forgot to add that files initially uploaded via the ProxyShell exploit will be a minimum of 265 KB.
This is due to the ProxyShell exploit abusing the Mailbox Export function of Exchange Powershell.
PSTs have a minimum size of 265KB.
Thx to @testanull for the info!
This is due to the ProxyShell exploit abusing the Mailbox Export function of Exchange Powershell.
PSTs have a minimum size of 265KB.
Thx to @testanull for the info!
• • •
Missing some Tweet in this thread? You can try to
force a refresh