1/4 @CreamFinance was exploited in (one hack tx: etherscan.io/tx/0xa9a1b8ea2…), leading to the gain of ~$18.8M for the hacker.
2/4 The hack is made possible due to a reentrancy bug introduced by $AMP, which is an ERC777-like token and exploited to re-borrow assets during its transfer before updating the first borrow. 

3/4 Specifically, in the example tx, the hacker makes a flashloan of 500 ETH and deposit the funds as collateral. Then the hacker borrows 19M $AMP and makes use of the reentrancy bug to re-borrow 355 ETH inside $AMP token transfer(). Then the hacker self-liquidates the borrow. 
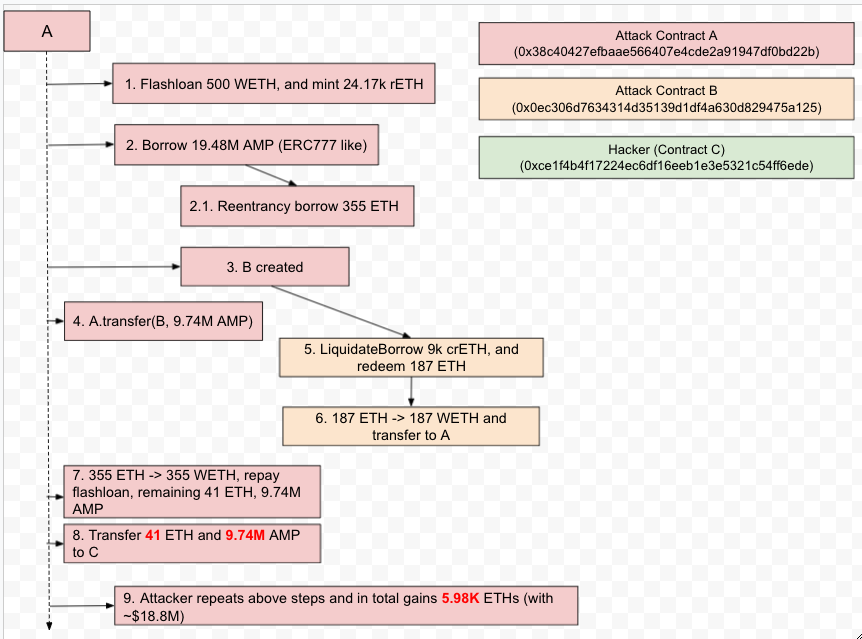
4/4 The hacker repeats the above process in 17 different txs and gains in total 5.98K ETHs (with ~$18.8M). The funds are still parked in 0xCE1F….6EDE. We are actively monitoring this address for any movement.
• • •
Missing some Tweet in this thread? You can try to
force a refresh