
It's awesome to see analysis of Lamberts and Equation Group tools. They're some of the most noteworthy findings in the short history of Cyber Threat Intelligence and we're doing a disservice by collectively ignoring their existence. Great work @runasand and @patrickwardle!
If you missed it, I'm sure the video will be up in the near future. In the meantime, here's Runa's blog on Green Lambert OS X
objective-see.com/blog/blog_0x68…
objective-see.com/blog/blog_0x68…
For additional (non-MacOS) background, here's an overview of the color-coded constellation of the Lambert's toolkit up to a point–
securelist.com/unraveling-the…
securelist.com/unraveling-the…
Since then additional flavors added to the rainbow include Gold, Orange, Purple, Violet, Silver...
Looking at this list I realize I should've called 'Tuxedo' Lambert (a blend of White Lambert code that drops Black Lambert) something more Skittles appropriate...
Looking at this list I realize I should've called 'Tuxedo' Lambert (a blend of White Lambert code that drops Black Lambert) something more Skittles appropriate...
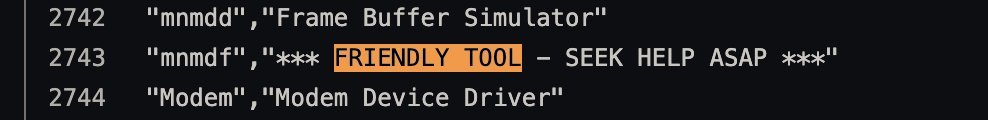
Another neat little tidbit, since we talking cross platform... GoldLambert is quite ancient but appears to have been originally coded for Unix and ported to Windows. It's also referenced in the Territorial Dispute driver_list.txt :) 
While Im ranting on Lamberts, it’s easy to look at the timeline and assume that folks latched onto them because of Vault7. But the first sighting of a Lambert was a font exploit discovered by Fireeye in 2014 alongside Black Lambert—
fireeye.com/blog/threat-re…
fireeye.com/blog/threat-re…
They are one of my favorite threat actors. They’re incredibly hard to track, well-segmented, OPSEC obsessive, and always rewarding to the keen analyst. That’s not to say they haven’t made opsec mistakes in the past but that’s a minor blemish on a superb record.
• • •
Missing some Tweet in this thread? You can try to
force a refresh





