[thread 🧵] ⚠️ nothing technical here, just sharing about my life
Since 2018, I’ve been creating or contributing to open-source projects, and I was wondering how many hours I spent of my personal time on this.
TL; DR: In 3 years, I squeezed in 1 year of additional free work.
Since 2018, I’ve been creating or contributing to open-source projects, and I was wondering how many hours I spent of my personal time on this.
TL; DR: In 3 years, I squeezed in 1 year of additional free work.
Usually working from 7pm to 9pm almost every day, and from 1pm to 7pm almost every Saturday. This equals to, roughly, 2000+ hours.
I wasn’t very consistent and there were times I was doing 2h/week, some times 20h/week w/o lunch break.
I wasn’t very consistent and there were times I was doing 2h/week, some times 20h/week w/o lunch break.
There were also times I switched personal and professional work slots in order to optimise both, but the number of hours is ~ the same
ADHD signals here? Dunno 🤷♂️
ADHD signals here? Dunno 🤷♂️

This sums to, roughly, 15 hours per week, for 3 years = 2340 hours.
« The traditional American business hours are 9:00 a.m. to 5:00 p.m., Monday to Friday, representing a workweek of five eight-hour days comprising 40 hours in total. » (wikipedia)
« The traditional American business hours are 9:00 a.m. to 5:00 p.m., Monday to Friday, representing a workweek of five eight-hour days comprising 40 hours in total. » (wikipedia)
What this means is I spent around 1 full year of traditional business hours in creating and contributing to open-source projects (this includes the rtfm and various research needed to accomplish those tasks).
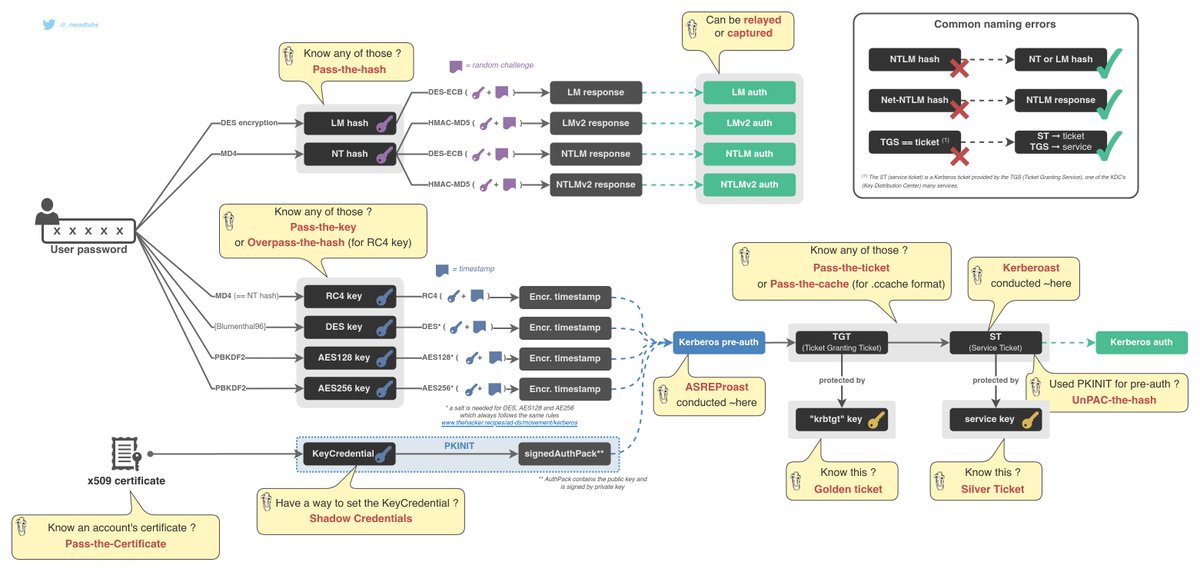
The main projects being thehacker.recipes and Exegol
The main projects being thehacker.recipes and Exegol
In 3 years, I worked an additional year, for free! This was never about the money, but this is huge!
This is awesome because I manage to do many things and I thrive in hyper-activity (another ADHD signal? 🤷♂️)
This is awesome because I manage to do many things and I thrive in hyper-activity (another ADHD signal? 🤷♂️)
But rest assured, there are downsides to this, including, but not limited to: sport ↘️, shitty diet ↗️, non-infosec-related-activites ↘️, social interactions ↘️, bad sleep ↗️
TL; DR: this is not good for my mental and physical health.
TL; DR: this is not good for my mental and physical health.
I noticed the downsides almost 1.5 years ago but didn’t change a thing. Impostor syndrome + infosec addiction + big professional challenges (+ ADHD?) + more and more support (awesome comments and DMs ❤️ ) kept me going.
Many friends told me to open some kind of ko-fi, patreon, tipeee, or somthing… I’m still hesitating. I’d be happy to be sponsored by orgs that rely on my contributions and show support, but uncomfortable to be backed up by people’s own hard earned money
And I think the feeling I described is very common and shared by many infosec contributors.
I’m not about to drop everything and go live in the mountains, but I wanted to share this, this is what’s Twitter for isn’t it?
I just need to find an equilibrium, for my own health and sanity. I’ve been struggling to find that equilibrium for a year now. But I guess I’ll find it one day 🤷♂️
I guess this answers what I’m asked the most: « how do you do all this? Where do you find the time? »
Well there is no magic, here is how.
On top of that, I’m not the smartest guy in the room. I compensate my lack of « intelligence » with time and effort.
Well there is no magic, here is how.
On top of that, I’m not the smartest guy in the room. I compensate my lack of « intelligence » with time and effort.
I think that’s it. I don’t have much else to share about this right now. I just wanted to share my thoughts 💭
Thank you (I guess?) for reading all this, see you really soon for some technical and infosec-related content 🙂
Thank you (I guess?) for reading all this, see you really soon for some technical and infosec-related content 🙂
• • •
Missing some Tweet in this thread? You can try to
force a refresh