[#thread 🧵] For this 20th day of #CyberAdvent we'll be talking about the Local Admin Password Solution #LAPS of Microsoft, and how it can be used to reduce the risk of network pivoting of attackers.
[#thread 🧵(2/6)] One of the common vulnerabilities found in Windows domains is a distributed local administrator on the workstations (sometimes even servers). This means that if an attacker compromises one machine, all the machines with the same administrator password are owned.
[#thread 🧵(3/6)] The attacker can then connect to all the other machines of the network using LM:NT hashes found on one compromised host! 😅
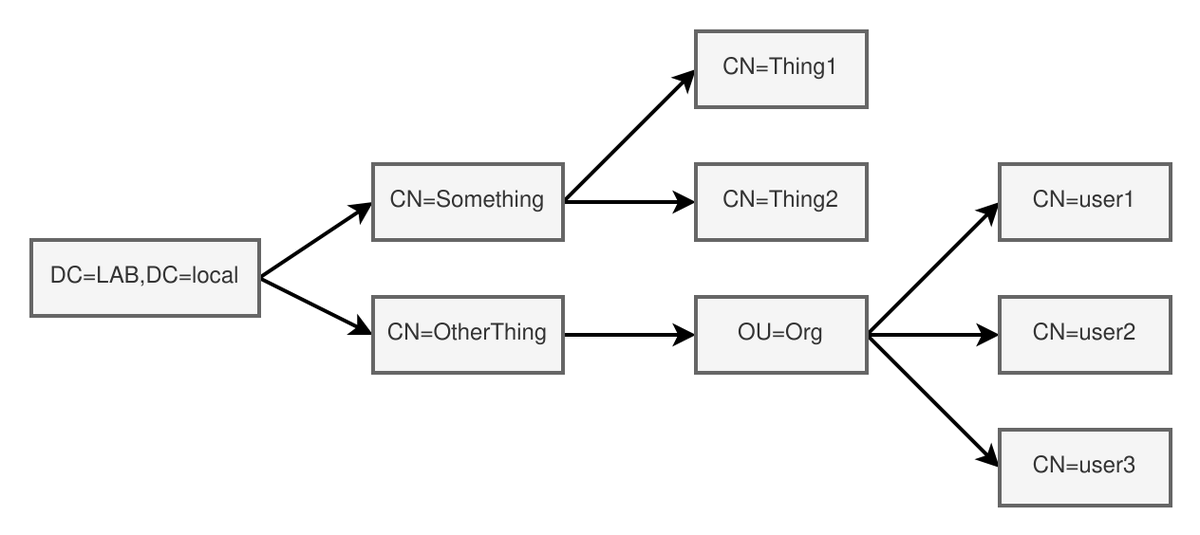
[#thread 🧵(4/6)] To read LAPS passwords, you need either:
▶️ Account with ExtendedRight or GenericRead to get LAPS passwords
▶️ Account with ExtendedRight or GenericWrite to set LAPS passwords
▶️ Domain Admin privileges
▶️ Account with ExtendedRight or GenericRead to get LAPS passwords
▶️ Account with ExtendedRight or GenericWrite to set LAPS passwords
▶️ Domain Admin privileges
[#thread 🧵(5/6)] If you are attacking from a Windows computer, you can use @pentest_swissky's SharpLAPS tool to extract machine passwords from LDAP with a privileged account:
github.com/swisskyrepo/Sh…
github.com/swisskyrepo/Sh…
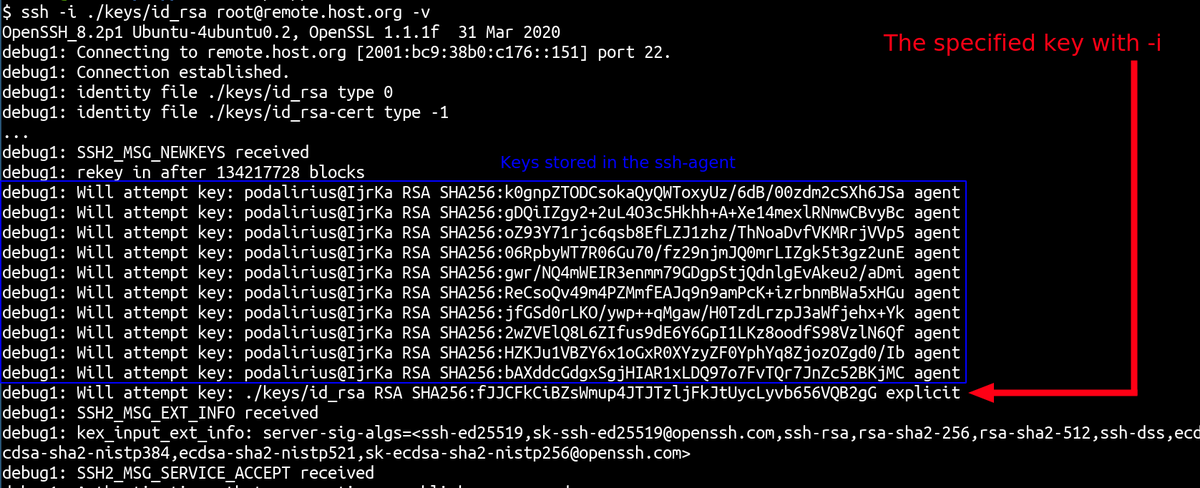
[#thread 🧵(6/6)] If you are attacking from a Linux computer, you can use my pyLAPS tool to extract machine passwords from LDAP with a privileged account:
github.com/p0dalirius/pyL…
github.com/p0dalirius/pyL…
• • •
Missing some Tweet in this thread? You can try to
force a refresh