🚨MAJOR INVESTIGATION: uncovering #GeckoSpy.
An espionage operation using #Pegasus spyware against #Thailand's pro-democracy movement.
THREAD on our findings 1/
Our @citizenlab collaborators: @iLawFX & @DigitalReachSEA w/validation by @AmnestyTech
citizenlab.ca/2022/07/geckos…



An espionage operation using #Pegasus spyware against #Thailand's pro-democracy movement.
THREAD on our findings 1/
Our @citizenlab collaborators: @iLawFX & @DigitalReachSEA w/validation by @AmnestyTech
citizenlab.ca/2022/07/geckos…



2/ In 2020, #Thailand's government triggered pro-democracy protests by disbanding a popular opposition party.
Protests continued into 2021, and were met with repression & violence.
Key figures were harassed, arrested & jailed.
Now, we know many were hacked, too.
Protests continued into 2021, and were met with repression & violence.
Key figures were harassed, arrested & jailed.
Now, we know many were hacked, too.
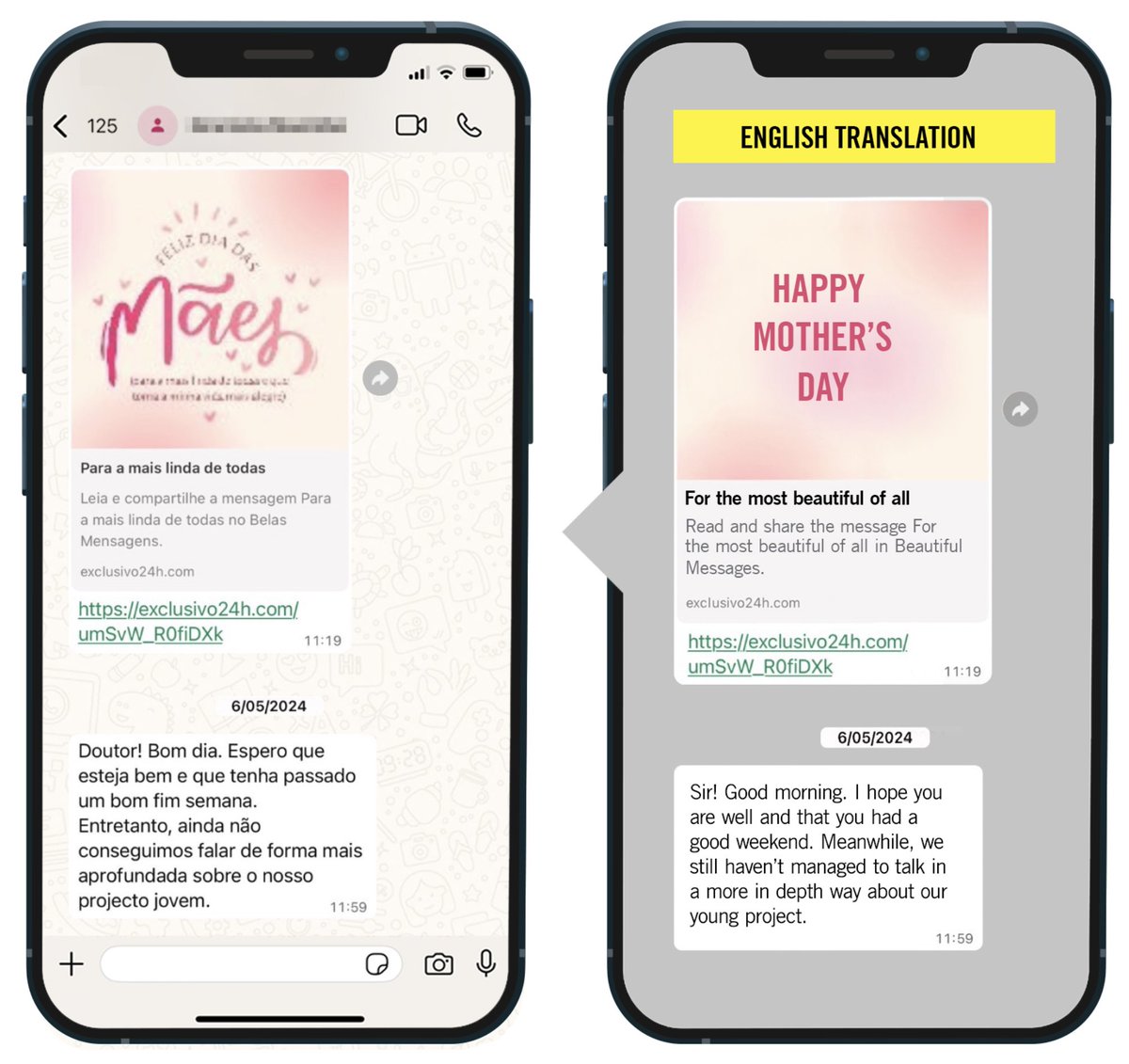
3/ The #GeckoSpy investigation began in Nov 2021... when @Apple notified users likely targeted w/#NSOGroup’s FORCEDENTRY exploit.
Multiple activists in #Thailand received them.
Some got in touch with us @citizenlab & our collaborators including @iLawFX & @DigitalReachSEA
Multiple activists in #Thailand received them.
Some got in touch with us @citizenlab & our collaborators including @iLawFX & @DigitalReachSEA

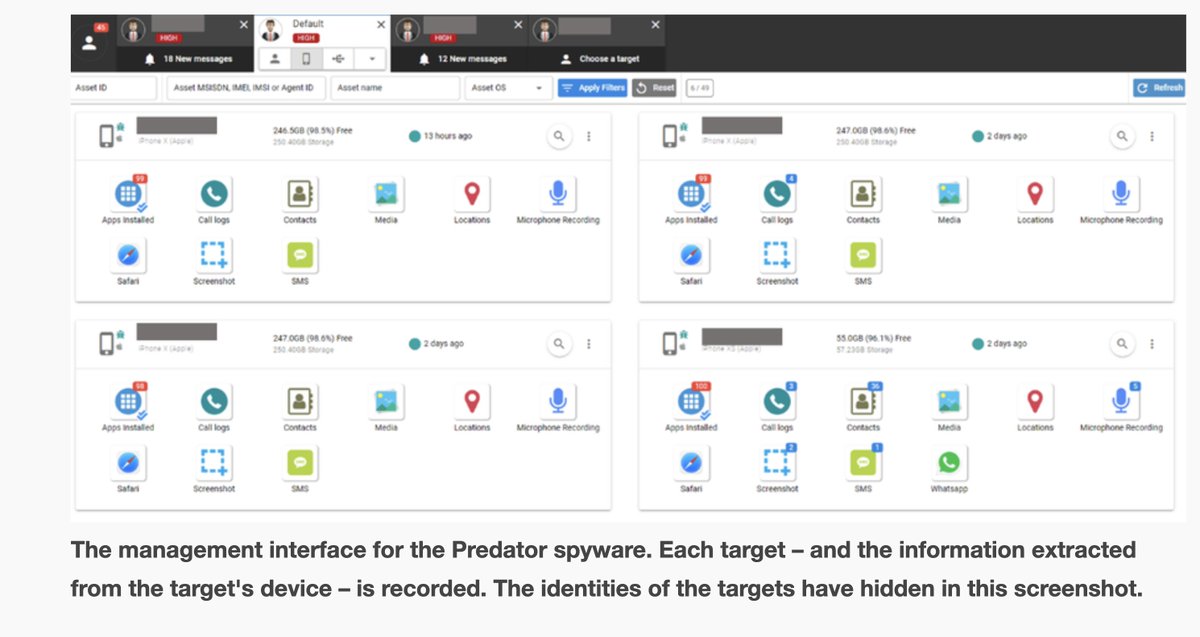
4/ Once notification recipients got in touch, forensic artifacts were consensually collected & analyzed.
The investigation then expanded to associates & other likely #Pegasus targets.
I cannot overstate the importance of @apple's notifications in focusing the initial process.
The investigation then expanded to associates & other likely #Pegasus targets.
I cannot overstate the importance of @apple's notifications in focusing the initial process.
4/ The #Pegasus hacking came in waves. Some pauses were probably dictated by things outside #Thailand.
Like the #PegasusProject publication, our disclosure of #ForcedEntry & @Apple's patch... and those notifications.
Other sequences of infection have a contextual explanation...
Like the #PegasusProject publication, our disclosure of #ForcedEntry & @Apple's patch... and those notifications.
Other sequences of infection have a contextual explanation...

5/ In many cases, #Pegasus infections in #Thailand matched protest & political activities.
Our collaborators @iLawFX & @DigitalReachSEA have a detailed report, including a table juxtaposing infections & protest events.
REPORT: freedom.ilaw.or.th/en/report-para…



Our collaborators @iLawFX & @DigitalReachSEA have a detailed report, including a table juxtaposing infections & protest events.
REPORT: freedom.ilaw.or.th/en/report-para…




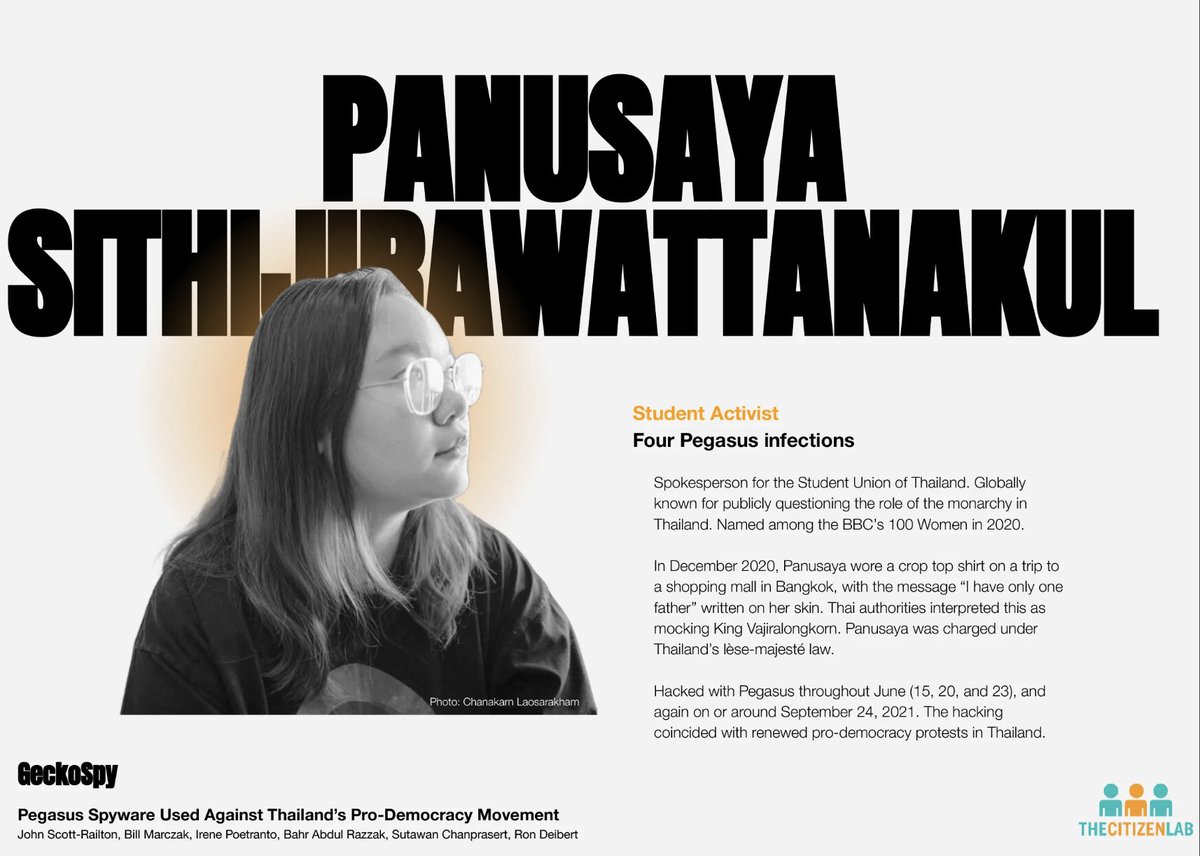
6/ Some #Pegasus victims are well known. Like Panusaya Sithijirawattanakul.
She once wore a crop top w/“I have only one father”
written on her skin. Went w/friends the mall for ice cream.
Thai authorities interpreted this as mocking the king, & charged her with lèse-majesté.

She once wore a crop top w/“I have only one father”
written on her skin. Went w/friends the mall for ice cream.
Thai authorities interpreted this as mocking the king, & charged her with lèse-majesté.


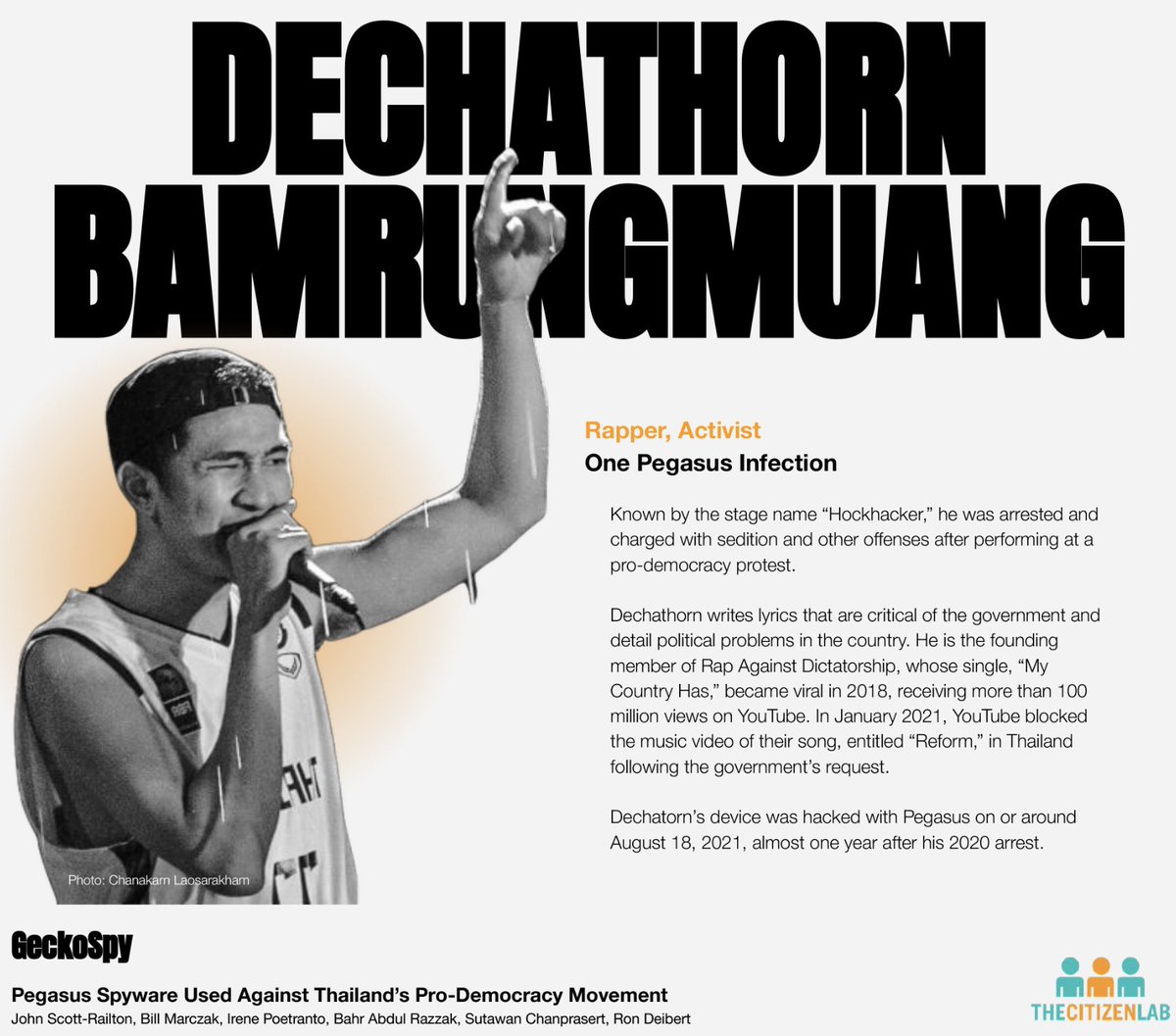
7/ High profile activists weren't the only category of #Pegasus victims.
Famous actress @charoenpura & rapper @DechathornHK were also infected.
Both were visible supporters of the pro-democracy movement.

Famous actress @charoenpura & rapper @DechathornHK were also infected.
Both were visible supporters of the pro-democracy movement.

8/ Also infected? Individuals with little public profile, but who played an important support role in protests, or fundraising.
A picture emerges: a #Pegasus operator seeking detailed information about the protest movement... in some cases guided by non public information.
A picture emerges: a #Pegasus operator seeking detailed information about the protest movement... in some cases guided by non public information.
9/ Who is behind the hacking? We @citizenlab aren't making a conclusive attribution.
But it's worth nothing that we've seen #Pegasus operators with a #Thailand nexus since 2014.
And there's a lot of circumstantial evidence...

But it's worth nothing that we've seen #Pegasus operators with a #Thailand nexus since 2014.
And there's a lot of circumstantial evidence...


10/ When you read the @iLawFX & @DigitalReachSEA report, it's clear: the entity responsible for the hacking has a detailed & obsessive focus on voices calling for democracy and reform of the monarchy in #Thailand.
https://twitter.com/iLawFX/status/1548893330645598208
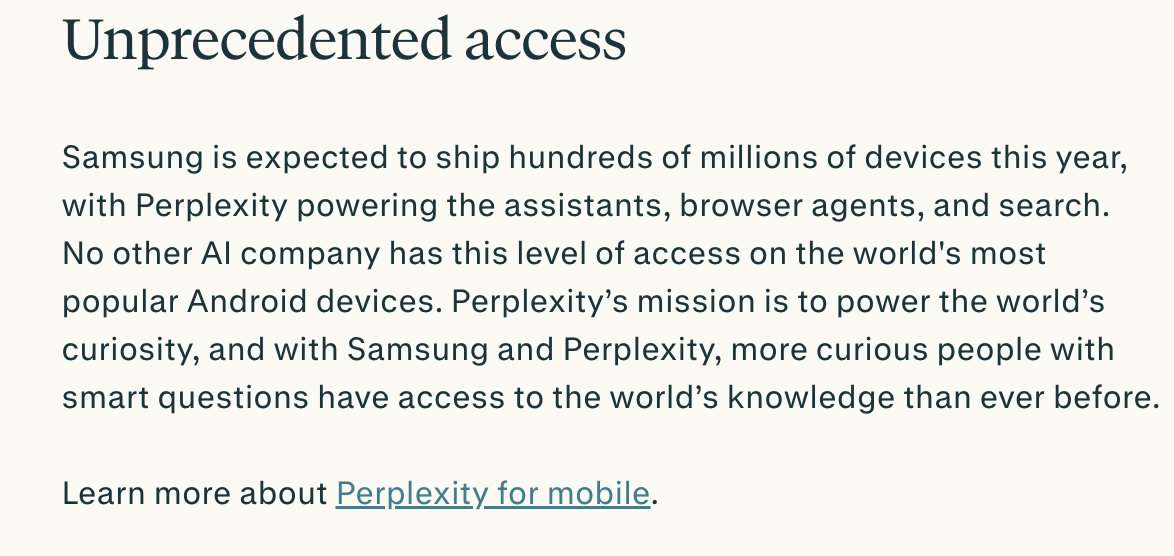
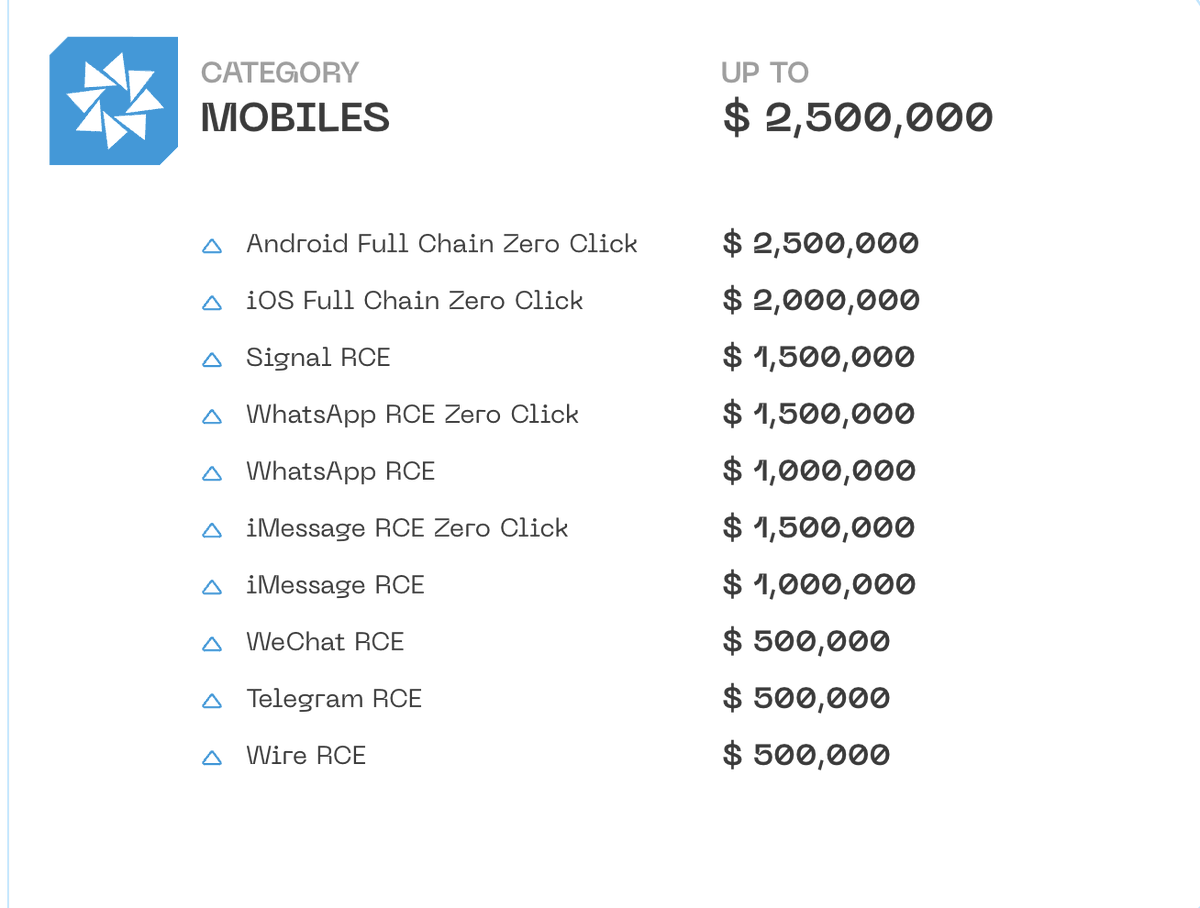
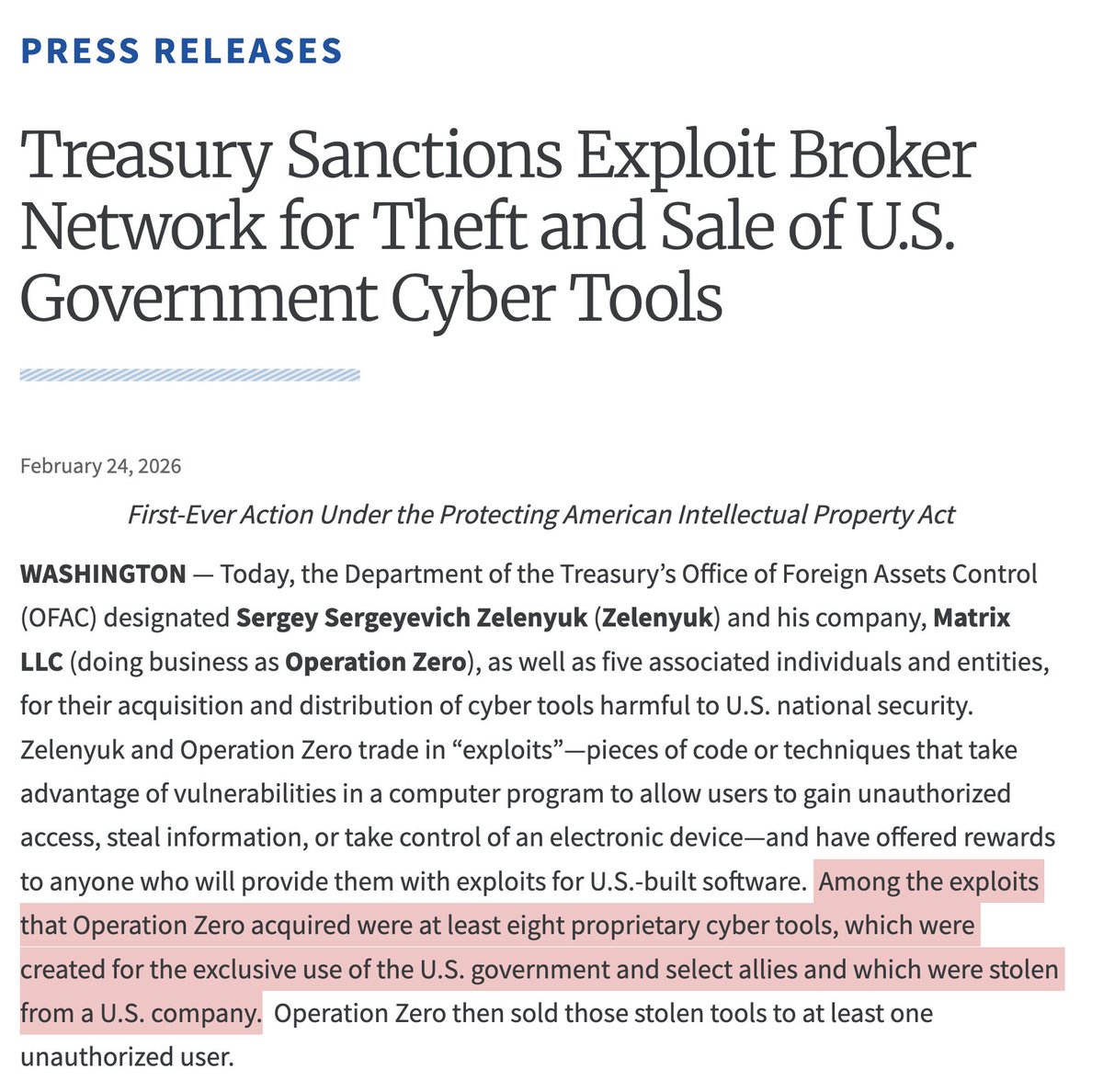
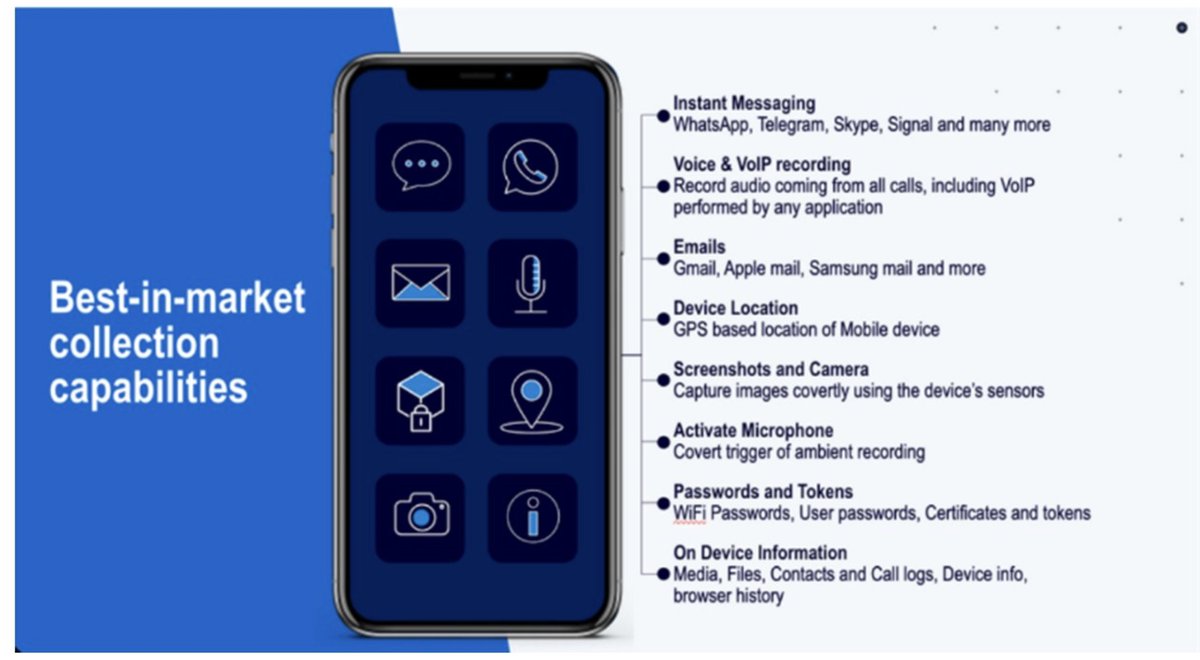
11/ My @citizenlab colleague @billmarczak explains that the #Pegasus hacking in #Thailand relied on zero-click vulnerabilities👇
Translation: *nothing* regular phone users could have done to protect themselves.
Translation: *nothing* regular phone users could have done to protect themselves.
https://twitter.com/billmarczak/status/1548884562545037312
12/ This investigation only happened because victims came forward & participated.
#Pegasus can make people feel powerless about digital security, yet they acted to reclaim some agency & are now helping to shed light on the secret mechanics of repression.
It's deeply inspiring.
#Pegasus can make people feel powerless about digital security, yet they acted to reclaim some agency & are now helping to shed light on the secret mechanics of repression.
It's deeply inspiring.
13/ Special thanks to the team at @AmnestyTech, which independently analyzed a sample of indicators in this case & confirmed Pegasus infections using their distinct tools and methods. 
14/ This investigation was a team production, ranging from the incredible work done by our collaborators @iLawFX and @DigitalReachSEA, civil society groups that prefer to remain unnamed, and the @citizenlab team including👇

https://twitter.com/citizenlab/status/1548868899889942529

• • •
Missing some Tweet in this thread? You can try to
force a refresh