1/ #IR-Tip: One of the (many) tasks to do after a compromise of an (AD) network is to change ALL passwords (from users to service accounts).
This step is listed as #1 on the excellent "post compromise active directory checklist" from @UK_Daniel_Card (👏). 🧵
#CyberSecurity
This step is listed as #1 on the excellent "post compromise active directory checklist" from @UK_Daniel_Card (👏). 🧵
#CyberSecurity

2/ Trust is good, control is better, right?
Although we tell our customers repeatedly how fundamental a password change is, we have had more than one case where not all passwords were changed (intentionally or unintentionally), sometimes resulting of the re-entering of TAs.
Although we tell our customers repeatedly how fundamental a password change is, we have had more than one case where not all passwords were changed (intentionally or unintentionally), sometimes resulting of the re-entering of TAs.
3/ Here is a simple example of how @velocidex Velociraptor can be used to check if the passwords have been changed.
The following command find the DC(s) on the network (without having to consult our notes - yep, I'm bad at remembering things):
nltest /DSGETDC:
The following command find the DC(s) on the network (without having to consult our notes - yep, I'm bad at remembering things):
nltest /DSGETDC:
4/ We select the DC (or one of the DC's) within Velociraptor, open the PowerShell prompt and run the following command: 

5/ Import modules ActiveDirectory
Get-ADUser -Filter 'Enabled -eq $True' -Properties PasswordLastSet | Where-Object {$_.PasswordLastSet -lt (Get-Date).adddays(-5)} | select Name,SamAccountName,PasswordLastSet | Export-CSV -Path "C:\Temp\passwords.csv" -notypeinformation
Get-ADUser -Filter 'Enabled -eq $True' -Properties PasswordLastSet | Where-Object {$_.PasswordLastSet -lt (Get-Date).adddays(-5)} | select Name,SamAccountName,PasswordLastSet | Export-CSV -Path "C:\Temp\passwords.csv" -notypeinformation
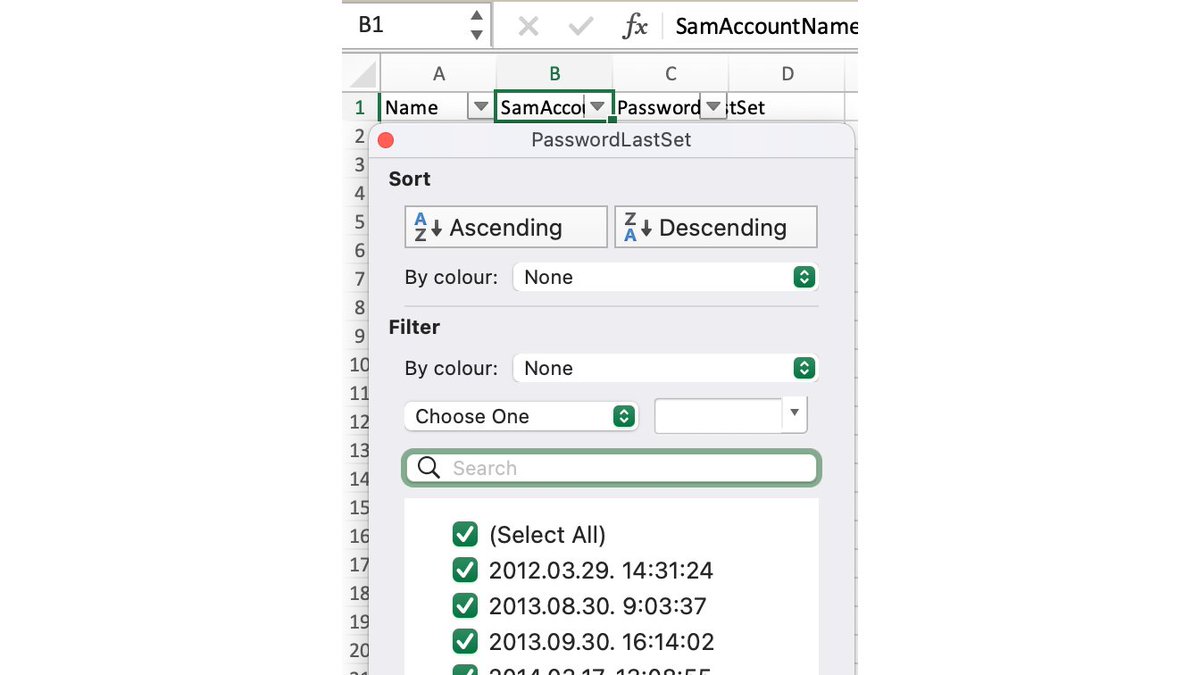
6/ The command checks the PasswordLastSet attribute and writes the usernames to a CSV file that have not changed their passwords since N days.
The following excerpt is from an actual IR where it is evident that not all PW has been changed.
A great check and easy to perform. 💪
The following excerpt is from an actual IR where it is evident that not all PW has been changed.
A great check and easy to perform. 💪
• • •
Missing some Tweet in this thread? You can try to
force a refresh