#ESETresearch reveals new findings about POLONIUM, an APT group that has targeted more than a dozen organizations in Israel 🇮🇱 since at least September 2021, using at least seven different custom backdoors.
welivesecurity.com/2022/10/11/pol…
1/6
welivesecurity.com/2022/10/11/pol…
1/6
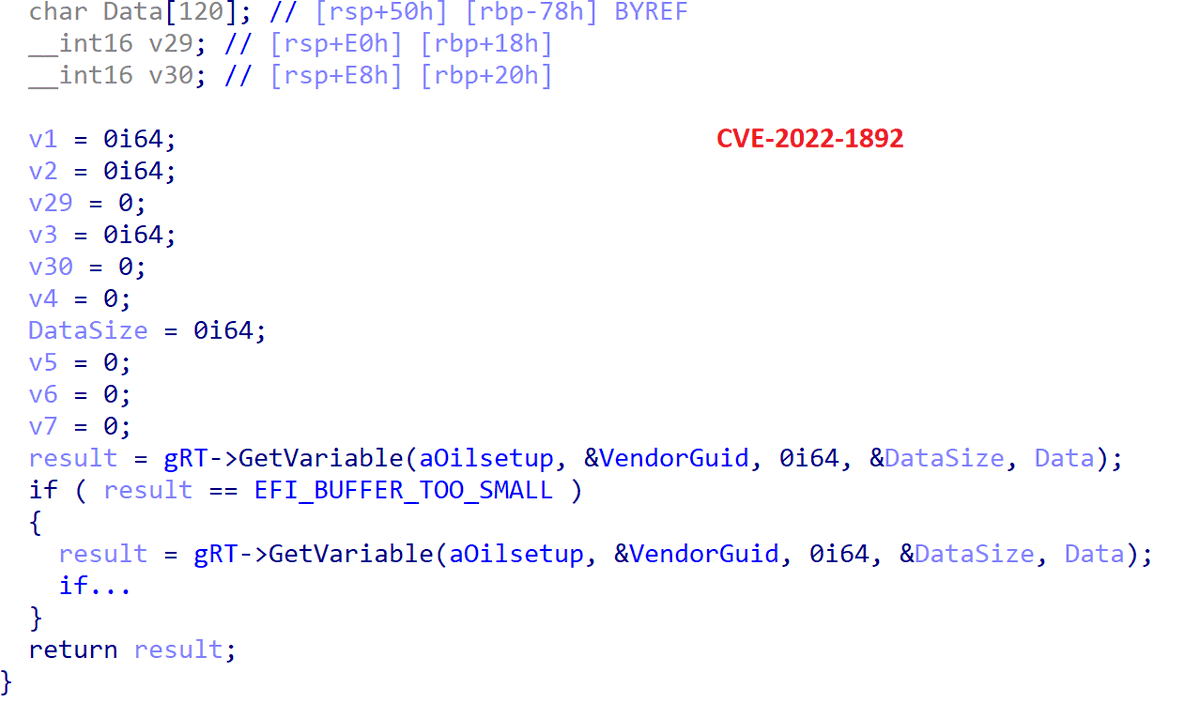
Five of the seven described #POLONIUM backdoors were previously undocumented. At the time of writing our blogpost, the latest one (PapaCreep) was still being used. It is also the first one not written in C# or PowerShell. 2/6 

Interestingly, the commands of the FlipCreep backdoor do exactly the opposite of what’s expected. We don’t know if this was a mistake, but UPLOAD actually downloads files from the FTP server to the victim, and DOWNLOAD uploads files. 3/6 

Several POLONIUM tools abuse cloud services such as #Dropbox, #Mega and #OneDrive for C&C communications. The group has also used several custom modules to spy on its targets – taking screenshots, webcam snapshots, monitoring keystrokes in Hebrew and Arabic. 4/6
Not much public information is available about POLONIUM, its initial compromise vector is unknown. However, some victims of this campaign had their Fortinet VPN account credentials leaked in September 2021 and were made available online. 5/6
The POLONIUM research was presented at the end of September 2022 at @virusbtn #VB2022 in Prague 🇨🇿. IoCs are available on ESET GitHub: github.com/eset/malware-i… 6/6
• • •
Missing some Tweet in this thread? You can try to
force a refresh