
#Sidewinder #APT
It seems that #Indian APTs have been raging war on #Pakistan with the same payloads over and over again. Meanwhile, Pakistani #Government and #Military is either helpless or over occupied. Following is another new sample that goes ages back.
It seems that #Indian APTs have been raging war on #Pakistan with the same payloads over and over again. Meanwhile, Pakistani #Government and #Military is either helpless or over occupied. Following is another new sample that goes ages back.
A variant of this sample has attributed to #Sidewinder #APT by Govt. of Pak. The #malware is deployed using the shared image in a #phishing email using a similar methodology to that of 
https://twitter.com/WLamiasi/status/1355787245358362626?s=20
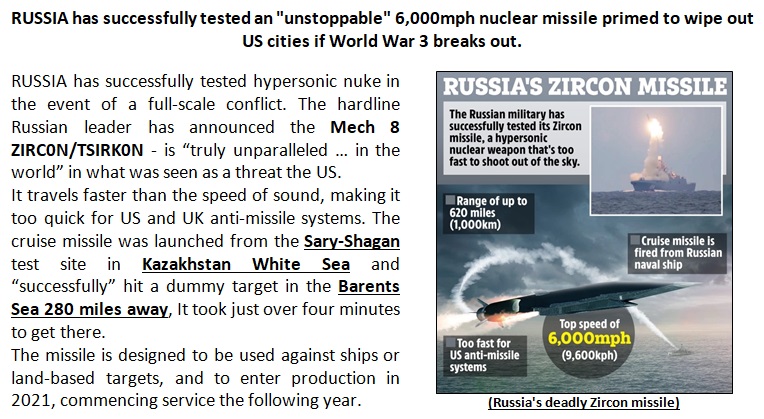
DOCX MD5: 2a6249bc69463921ada1e960e3eea589 Mech 8 ZIRC0N-TSIRK0N.doc
#Exploit: hashcheck[.]xyz/PY8997/yrql/plqs
RTF MD5: 7c11d5125c3fb167cca82ff8b539e3c7 plqs
#C2: sportfunk[.]xyz/topaz/foti
CVE-2017-11882
#Exploit: hashcheck[.]xyz/PY8997/yrql/plqs
RTF MD5: 7c11d5125c3fb167cca82ff8b539e3c7 plqs
#C2: sportfunk[.]xyz/topaz/foti
CVE-2017-11882

Data Sent to C2
Name: @@PROCESSOR@@>Caption: Microsoft Windows 7 Professional >V:|||@@USER@@-@@HOSTNAME@@-@@guid??@@||||||@@[Two Char]|||[One digit]|||<<programfiles-folder>>?<<programfiles-folder>>?<<programfiles-folder>>?<<programfiles-folder>>?<<programfiles-folder>>?ÍÍÍÍÍÍÍÍÍ
Name: @@PROCESSOR@@>Caption: Microsoft Windows 7 Professional >V:|||@@USER@@-@@HOSTNAME@@-@@guid??@@||||||@@[Two Char]|||[One digit]|||<<programfiles-folder>>?<<programfiles-folder>>?<<programfiles-folder>>?<<programfiles-folder>>?<<programfiles-folder>>?ÍÍÍÍÍÍÍÍÍ
#Encryption
AES-256 Implementation for comm with C2
Mode: CBC
Key: 56 de 87 34 db ec 2d 78 66 23 98 3b ce 77 73 8e
IV: 0a 0b 0c 0d 0e 0f 09 08 07 06 05 04 03 02 01 ab
AES-256 Implementation for comm with C2
Mode: CBC
Key: 56 de 87 34 db ec 2d 78 66 23 98 3b ce 77 73 8e
IV: 0a 0b 0c 0d 0e 0f 09 08 07 06 05 04 03 02 01 ab
#Sidewinder #APT skillset seems a bit better than that of other #Indian counterparts in that it uses COM objects to perform operations and undocumented Windows APIs and has much better phishing subjects.
#Yara #SIDEWINDER #VTYREI Rule
rule SIDEWINDER_vtyrei_dll
{
meta:
author = "Will Lamiasi"
strings:
$h1 = {0a 0b 0c 0d 0e 0f 09 08 07 06 05 04 03 02 01 ab}
$h2 = {87 34 db ec 2d 78 66 23 98 3b ce 77 73 8e}
condition:
($h1 or $h2)
}
rule SIDEWINDER_vtyrei_dll
{
meta:
author = "Will Lamiasi"
strings:
$h1 = {0a 0b 0c 0d 0e 0f 09 08 07 06 05 04 03 02 01 ab}
$h2 = {87 34 db ec 2d 78 66 23 98 3b ce 77 73 8e}
condition:
($h1 or $h2)
}
Older #Sidewinder #Vtyrei #C2:
RTF from hashcheck.xyz/KB4523/update/…
Data sent to createlist.xyz/topaz/foti
Attribution based on download1.fbr.gov.pk/Docs/202012917…
RTF from hashcheck.xyz/KB4523/update/…
Data sent to createlist.xyz/topaz/foti
Attribution based on download1.fbr.gov.pk/Docs/202012917…
#Sidewinder #Vyrei #IOCs:
2a6249bc69463921ada1e960e3eea589
7c11d5125c3fb167cca82ff8b539e3c7
c03e8a6caf31b95928a8bfc4ec0ece1c
1dc5d8bd474e922439546f4e4e8c9b7c
d2029c158d4ae4ccb3f062148d27c8f2
5d0f25a6c9fead3dfbd606ae9831cfa4
75fadd4e6e9bfe5a1547805ab9a09407
2a6249bc69463921ada1e960e3eea589
7c11d5125c3fb167cca82ff8b539e3c7
c03e8a6caf31b95928a8bfc4ec0ece1c
1dc5d8bd474e922439546f4e4e8c9b7c
d2029c158d4ae4ccb3f062148d27c8f2
5d0f25a6c9fead3dfbd606ae9831cfa4
75fadd4e6e9bfe5a1547805ab9a09407
590bf4ef8cc49dd2753cf048bb9a6d60
b9a62d78b7f64b194dc71fb7366a5104
ae4997c6942820fd06066e36425cfb58
b9a62d78b7f64b194dc71fb7366a5104
ae4997c6942820fd06066e36425cfb58
@threadreaderapp unroll
• • •
Missing some Tweet in this thread? You can try to
force a refresh



