I am thrilled to announce #BloodHoundEnterprise, which will be released in Summer of 2021!
Learn more: specterops.io/bloodhound-ent…
View our announcement webinar: specterops.zoom.us/webinar/regist…
A thread of major points about BloodHound Enterprise:
Learn more: specterops.io/bloodhound-ent…
View our announcement webinar: specterops.zoom.us/webinar/regist…
A thread of major points about BloodHound Enterprise:

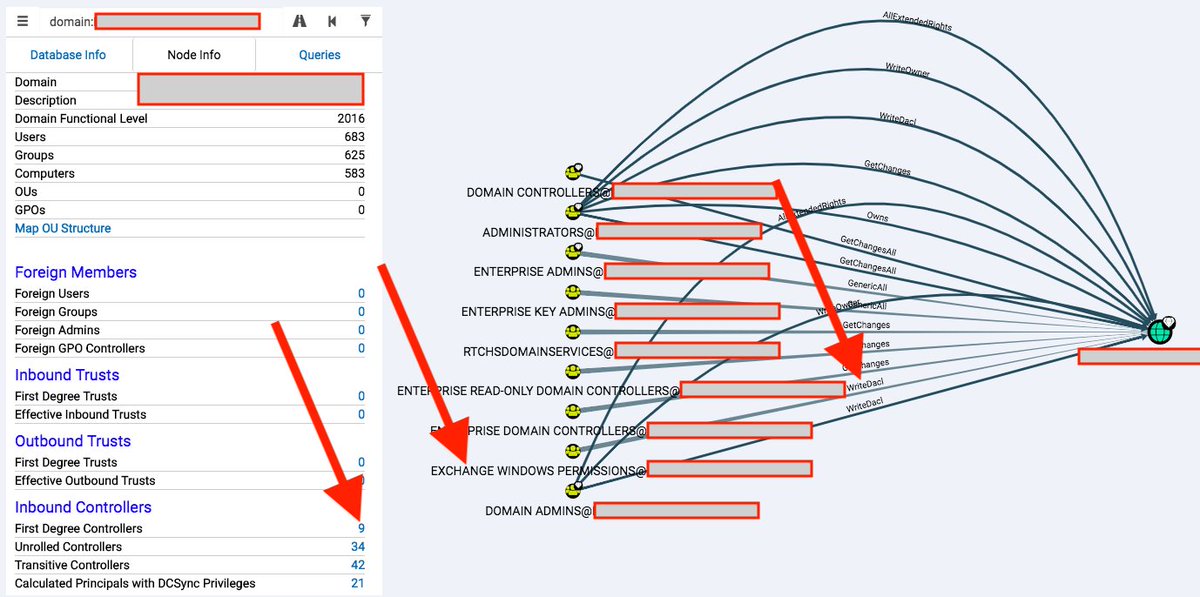
Once an attacker has access to Active Directory, it's virtually guaranteed they can find an attack path resulting in the compromise of a Tier 0 asset (Domain Admin). Owning Tier 0 means owning AD. Owning AD means owning the organization, all its data, users, processes, etc.
The scale, availability, and growth of those attack paths has exposed an enormous gap in how we try to secure Active Directory today. Organizations try (and fail) to fill that gap with technologies, products, and processes.
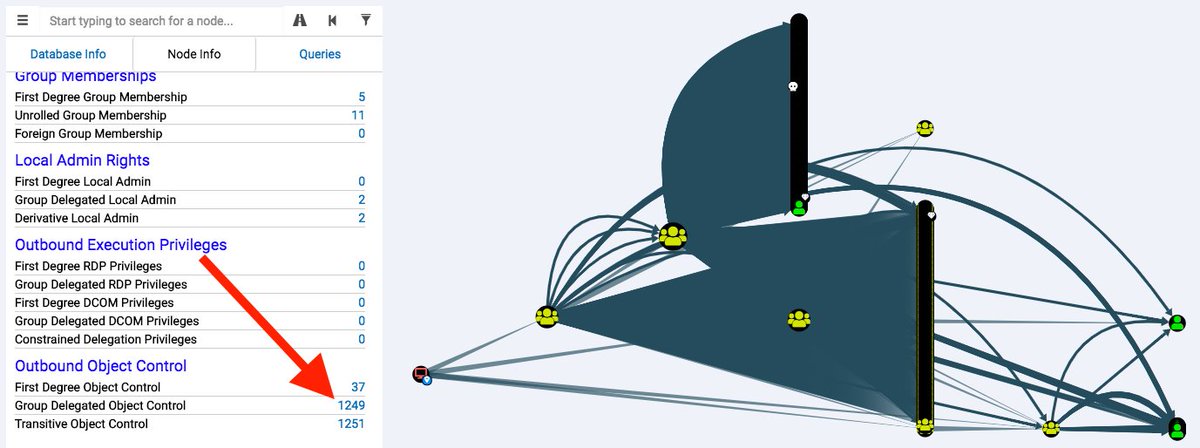
We think it's possible to fill that gap by quantifying the most critical choke points in AD. BloodHound Enterprise identifies and quantifies the most critical attack path choke points, enabling highly effective remediation with minimal effort within your existing architecture.
We call this methodology "Attack Path Management". At the core of that methodology is the Attack Path Topology, which prioritizes remediation actions based on attack path reduction.
What was once unknowable and invisible for the defender becomes clear, concise, and easily tracked over time. BloodHound Enterprise reports overall Tier 0 exposure (percentage of users w/ an attack path to Tier 0). 

Free and open source BloodHound isn't going anywhere. We are continuing research and development on FOSS BloodHound, which will remain free and open source forever. 

Want to know more?
Join the #BloodHound Slack: bloodhoundgang.herokuapp.com
There is a new channel dedicated to BHE, #bloodhoundenterprise
Join the #BloodHound Slack: bloodhoundgang.herokuapp.com
There is a new channel dedicated to BHE, #bloodhoundenterprise
• • •
Missing some Tweet in this thread? You can try to
force a refresh