Marcus Willett, @GCHQ's first director of cyber, assesses the SolarWinds intrusion. "... it is neither accurate nor sensible for US commentators to characterise it as an act of war requiring warlike retaliation" iiss.org/blogs/survival… 

An interesting reminder from Willett: espionage generates transparency. "Attempts to steal state secrets in peacetime are internationally tolerated because, among other things, they can reduce the chance of a misunderstanding that could lead to a real conflict." 

Another key point: attribution is easier than people think. "Cyber-capable states have for some time been able to confidently identify perpetrators of attacks, though they have often hesitated to make those attributions public due to ... protecting sensitive intelligence sources"
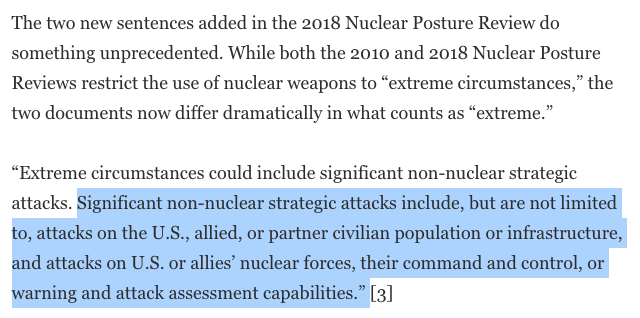
Willett: cyber norms need to define critical infrastructure narrowly. "states will inevitably consider a potential adversary’s critical networks a legitimate wartime target, and need to gain a technical presence on such networks during peacetime to prepare for that eventuality." 

Willett: focusing on state cyber operations misses the point. "Reinforcing basic cyber hygiene with new laws establishing disincentives to pay ransoms to cyber criminals – it is currently too convenient for companies simply to use their insurance to pay up ... would make sense" 

• • •
Missing some Tweet in this thread? You can try to
force a refresh