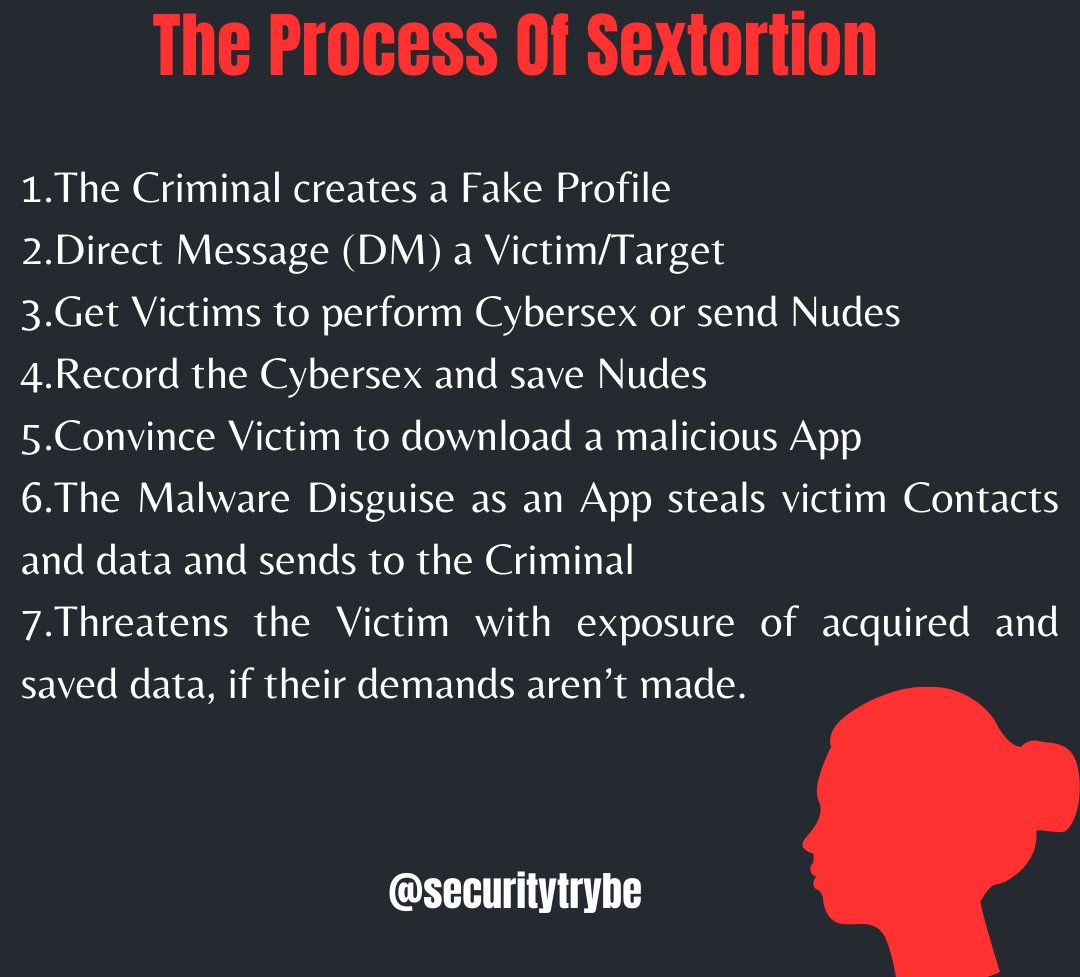
How To Deal With Sextortion
#CyberSecurity #CyberAttack #sextortion #Hacked #Security #cybersafety #community #cybercrime
#CyberSecurity #CyberAttack #sextortion #Hacked #Security #cybersafety #community #cybercrime

• • •
Missing some Tweet in this thread? You can try to
force a refresh