You've been asking me for a long time and finally I decided to write an ultimative thread on an advanced (and authorial, please note) cryptocurrency storage technology 😎
Read carefully, there will be only Spy-level trips 👇
Read carefully, there will be only Spy-level trips 👇
1/X
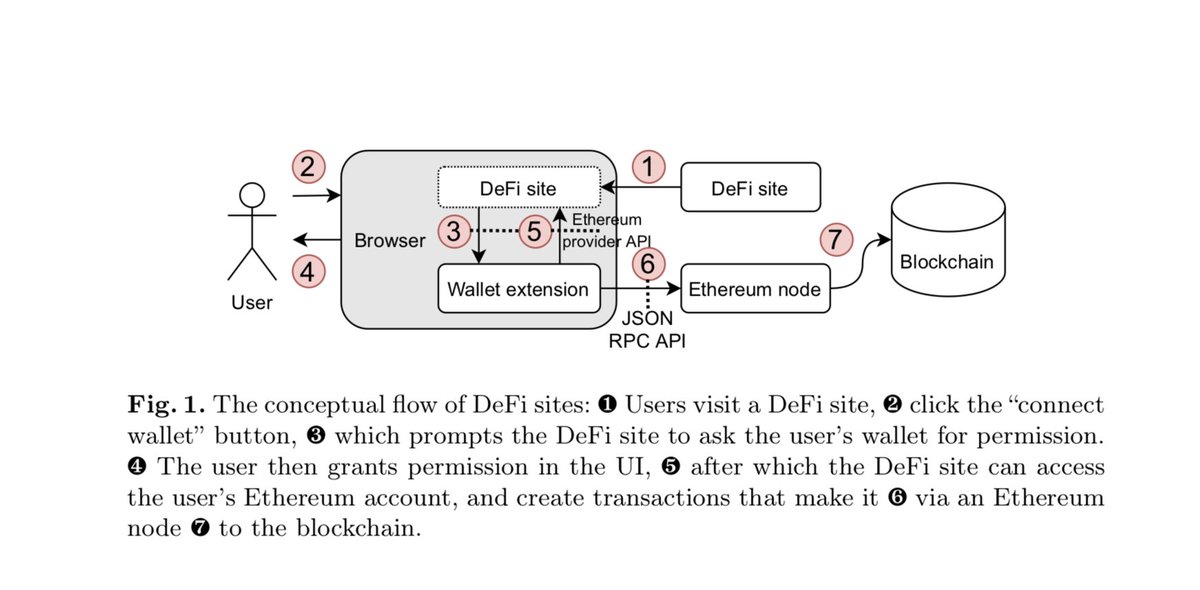
Understand that all sorts of blockchain.info, TrustWallet, MetaM/\sk and other wallets are just interfaces.
Understand that all sorts of blockchain.info, TrustWallet, MetaM/\sk and other wallets are just interfaces.
2/X
Consider cold wallets, personally I do not trust Ledger or Trezor. There is a hardcore version BitLox Ultimate, which is literally stuffed with security-related features, lets the traffic through Tor, and has several levels of encryption: bitlox.com/products/bitlo…
Consider cold wallets, personally I do not trust Ledger or Trezor. There is a hardcore version BitLox Ultimate, which is literally stuffed with security-related features, lets the traffic through Tor, and has several levels of encryption: bitlox.com/products/bitlo…
3/X
Or an ascetic cold card which is a good choice for those, who love simple and clear mechanics. coldcard.com
Or an ascetic cold card which is a good choice for those, who love simple and clear mechanics. coldcard.com
4/X
Make a cold wallet yourself. For example, from an old smartphone. You can also make a cold wallet with Electrum and let all the traffic through Tor. Know AirGap weak sides.
Make a cold wallet yourself. For example, from an old smartphone. You can also make a cold wallet with Electrum and let all the traffic through Tor. Know AirGap weak sides.
6/X
Check what are you signing, if we speak about ETH L1 L2, never use your main cold storage for casual work, but if you have to, always check if there are no allowance approve (which allows to drain your wallet) or proxy behind which mentioned function may be hiding.
Check what are you signing, if we speak about ETH L1 L2, never use your main cold storage for casual work, but if you have to, always check if there are no allowance approve (which allows to drain your wallet) or proxy behind which mentioned function may be hiding.
8/X
Never use your main cold storage and «Back Office PC» for casual work, but if you have to do it, use only open-source wallets like alphawallet.com, electrum.org, sparrowwallet.com
-
-
Never use your main cold storage and «Back Office PC» for casual work, but if you have to do it, use only open-source wallets like alphawallet.com, electrum.org, sparrowwallet.com
-
https://twitter.com/officer_cia/status/1516581048792289280
-
https://twitter.com/officer_cia/status/1516581048792289280
10/X
Accept as a fact that if the device falls into the hands of intruders, only custom capacitors can save your money (so that you can not get directly to the brains and read electric signals) and other things like self-destruction, epoxy, and so on.
Accept as a fact that if the device falls into the hands of intruders, only custom capacitors can save your money (so that you can not get directly to the brains and read electric signals) and other things like self-destruction, epoxy, and so on.
11/X
That is, ideally, you can not allow physical contact in any case. You can use special logic bombs or logic gates, extra passwords that trigger some kind of security action, alert events on your address via tenderly.co or using 2/3 multi-sig.
That is, ideally, you can not allow physical contact in any case. You can use special logic bombs or logic gates, extra passwords that trigger some kind of security action, alert events on your address via tenderly.co or using 2/3 multi-sig.
12/X
One could also create a honeypot wallet and have a script that listens for tx originating from those addresses that alerts authorities, security companies and/or friends & family that you are under duress, perhaps even sending your location or last known location via GPS.
One could also create a honeypot wallet and have a script that listens for tx originating from those addresses that alerts authorities, security companies and/or friends & family that you are under duress, perhaps even sending your location or last known location via GPS.
13/X
Always double check an address you've copied to the clipboard. There is an evil software existing which can replace an address in your clipboard to a very similar-looking address which has the same symbols in the beginning/end as your address.
-
Always double check an address you've copied to the clipboard. There is an evil software existing which can replace an address in your clipboard to a very similar-looking address which has the same symbols in the beginning/end as your address.
-
https://twitter.com/officer_cia/status/1491920415387574275
14/X
Be aware of modern attack methods, carefully read step-by-step my Guide and a Compendium, you don't need a deep understanding of how hacks work exactly but that's important to know how does it looks like to be a victim:
- github.com/OffcierCia/Cry…
- graph.org/All-known-smar…
Be aware of modern attack methods, carefully read step-by-step my Guide and a Compendium, you don't need a deep understanding of how hacks work exactly but that's important to know how does it looks like to be a victim:
- github.com/OffcierCia/Cry…
- graph.org/All-known-smar…
15/X
Cold wallet attacks list:
- adatainment.com/index.php
- ieeexplore.ieee.org/document/92847…
- cossacklabs.com/blog/crypto-wa…
- cipherblade.com/blog/list-of-b…
- arxiv.org/pdf/2108.14004…
- bloom.co/blog/6-ways-a-…
- phishfort.com/blog/web3-phis…
- arxiv.org/pdf/2204.01487…
- arxiv.org/pdf/2111.08893…
Cold wallet attacks list:
- adatainment.com/index.php
- ieeexplore.ieee.org/document/92847…
- cossacklabs.com/blog/crypto-wa…
- cipherblade.com/blog/list-of-b…
- arxiv.org/pdf/2108.14004…
- bloom.co/blog/6-ways-a-…
- phishfort.com/blog/web3-phis…
- arxiv.org/pdf/2204.01487…
- arxiv.org/pdf/2111.08893…
16/X
Study threat modeling and establish all possible threats even if they seem crazy to you. Being suspicion is always a good thing. After all, fake news only works best with those who carry it to their acquaintances, becoming a kind of donor.
Study threat modeling and establish all possible threats even if they seem crazy to you. Being suspicion is always a good thing. After all, fake news only works best with those who carry it to their acquaintances, becoming a kind of donor.
17/X
In the same way with attacks, very often you may try to be hacked through acquaintances, pretending to be acquaintances or acquaintances themselves. Always keep this in mind. This world is cruel and dangerous.
- usenix.org/system/files/1…
In the same way with attacks, very often you may try to be hacked through acquaintances, pretending to be acquaintances or acquaintances themselves. Always keep this in mind. This world is cruel and dangerous.
- usenix.org/system/files/1…
18/X
For deals use escrow and tx alarm clock and with special services like safient.io, sarcophagus.io, safehaven.io.
- github.com/OffcierCia/Cry…
- github.com/OffcierCia/Cry…
For deals use escrow and tx alarm clock and with special services like safient.io, sarcophagus.io, safehaven.io.
- github.com/OffcierCia/Cry…
- github.com/OffcierCia/Cry…
19/X
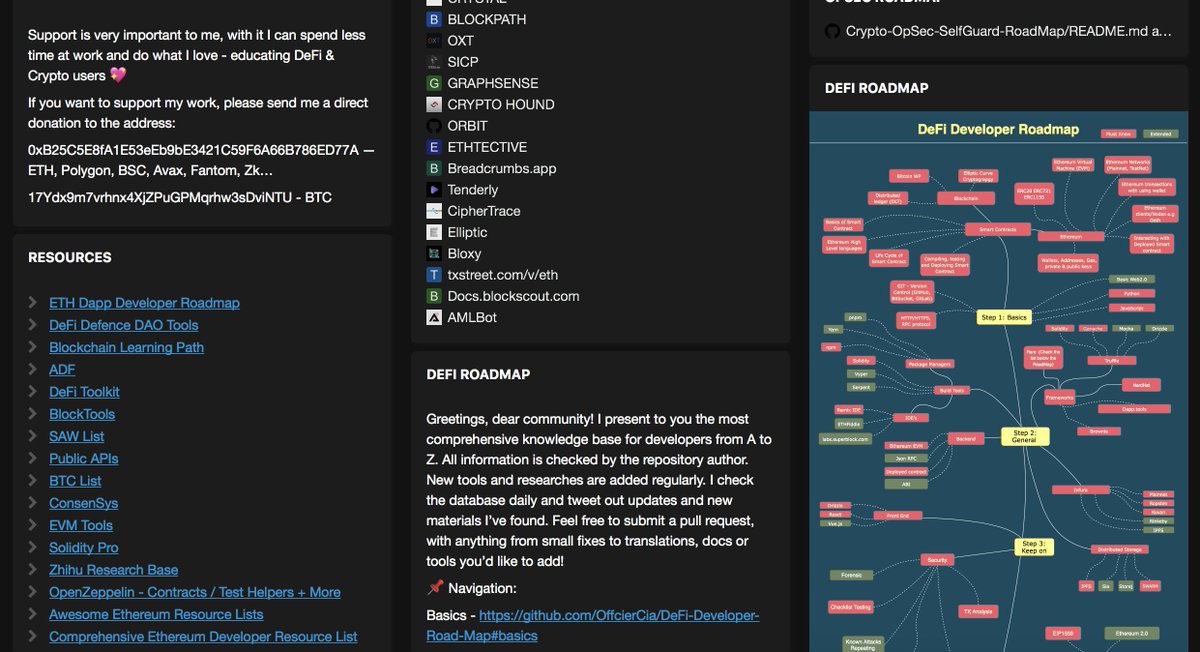
Use OpenSource password storage, self-hosted link system, reliable communication method, use #OpSec services, be aware of the latest anonymity and #privacy techniques:
- keepass.info
- obsidian.md
- github.com/jlopp/physical…
- docs.google.com/spreadsheets/d…
Use OpenSource password storage, self-hosted link system, reliable communication method, use #OpSec services, be aware of the latest anonymity and #privacy techniques:
- keepass.info
- obsidian.md
- github.com/jlopp/physical…
- docs.google.com/spreadsheets/d…
20/X
Counter-OSINT is important. Read about it here:
- t.me/officer_cia/200
-
Counter-OSINT is important. Read about it here:
- t.me/officer_cia/200
-
https://twitter.com/officer_cia/status/1444456564551819270v
No one service in the article, not one person paid me to mention them in the list unfortunately 😅.
This thread is an article I wrote a couple of days ago, read it here: graph.org/Key-principles…
This thread is an article I wrote a couple of days ago, read it here: graph.org/Key-principles…
Also check out my #OpSec guide github.com/OffcierCia/Cry…
Tip: use this tool when working w ith PDFs, CVs and such files 😎Or just use Qubes OS
https://twitter.com/officer_cia/status/1516440538999922694
Support is very important to me, with it I can spend less time at work and do what I love - educating #DeFi & #Crypto users 💖
If you want to support my work, please donate me to the address:
0xB25C5E8fA1E53eEb9bE3421C59F6A66B786ED77A — ERC20 & ETH (officercia.eth)
If you want to support my work, please donate me to the address:
0xB25C5E8fA1E53eEb9bE3421C59F6A66B786ED77A — ERC20 & ETH (officercia.eth)
Or make a paper wallet. Store it in reliable safe. That’s for the part of money, ideally is to split them.
Choose Water proof and Fire proof material for such purpose. Ideally is o use medical steel.
Why OpSec in general and Counter-OSINT in particular are important? Let’s take a look 👇
coindesk.com/business/2022/…
This guy used his real name and/or a phone number associated with his real identity. Bad OpSec and no Counter-OSINT been used… These techniques might saved him.
coindesk.com/business/2022/…
This guy used his real name and/or a phone number associated with his real identity. Bad OpSec and no Counter-OSINT been used… These techniques might saved him.
- Conduct an OSINT investigation against himself or hire an OSINTer
- All information that cannot be deleted by queries/abuse and complaints/attacks should be made unreadable by "obfuscation".
Example:
Visit my OpSec Map: github.com/OffcierCia/Cry…
- All information that cannot be deleted by queries/abuse and complaints/attacks should be made unreadable by "obfuscation".
Example:
https://twitter.com/officer_cia/status/1444456564551819270
Visit my OpSec Map: github.com/OffcierCia/Cry…
Thank you! Here you can track all my activities start.me/p/QRg5ad/offic…
• • •
Missing some Tweet in this thread? You can try to
force a refresh