Hello @Uber! We know breaches suck. Wanted to reach out and support with some interesting information on the #uberhack. If you need any more details, feel free to contact us.
#FightAgainstCybercrime
#FightAgainstCybercrime
On September 16, vx-underground posted screenshots with evidence of access to #Uber internal systems, including #SentinelOne, #Slack and #AWS. The screenshots have been attributed to the threat actor teapots2022. 
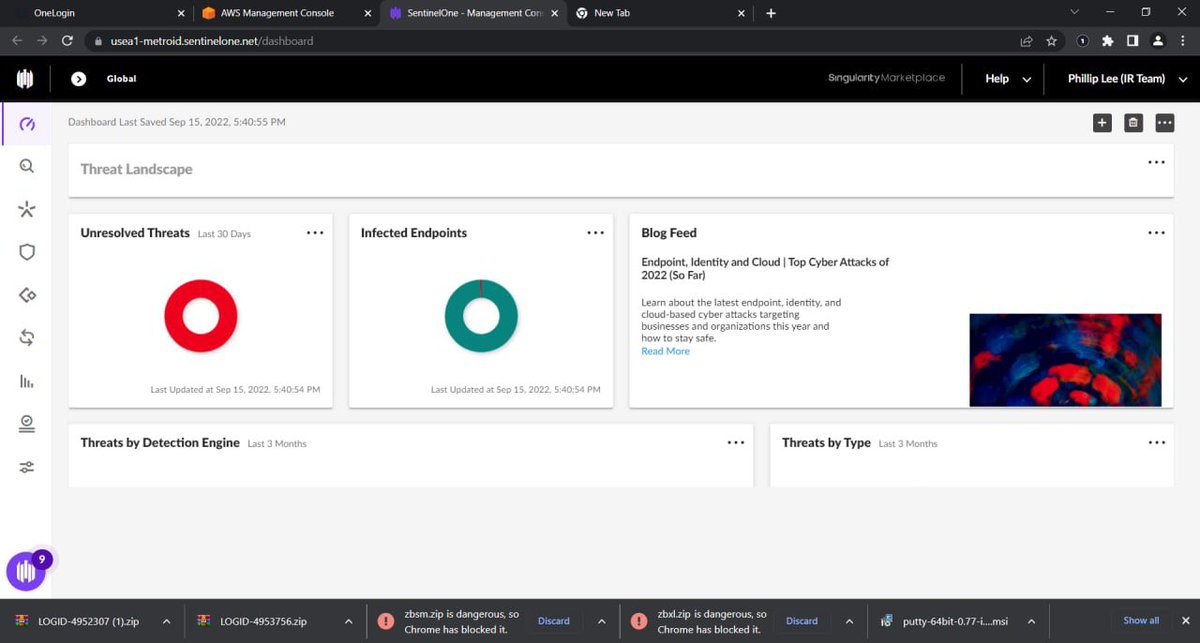
During Group-IB’s analysis of the screenshots, interesting artifacts have been found in the recently downloaded files tray. First 2 files are zip archives and have the same format: "LOGID-\d{7} with names LOGID-4952307" and "LOGID-4953756". 

The name format of these files allowed Group-IB researchers to identify them as logs from #stealers that were sold on one of the underground marketplaces.
Group-IB identified that these logs were put up for sale on September 12 and 14, which means that this was very fresh data, because the hack that utilized them was revealed from 15 to 16 September.
As shown below both of these logs contain authorization data for uber.onelogin.com — an identity and access management provider. These logs indicate that at least 2 Uber employees (from Indonesia and Brazil) have been infected by stealer #malware: Racoon and Vidar stealers. 

The version of @Uber hacking through the purchase of logs that contained data for authorization on uber.onelogin.com is confirmed by the same screenshot, where you can see that the very first tab in the browser is called "OneLogin". 

In addition to the #logs shown in the screenshot, the attacker could also have purchased logs to enable them to sort through all the accounts in search of accounts with privileged access to critical internal network resources.
These other logs also contained multiple access credentials to other resources, including Slack, Facebook, Google, Instagram etc. These credentials could have been used by the attacker to advance through Uber’s network using social engineering.
• • •
Missing some Tweet in this thread? You can try to
force a refresh