NEW RESEARCH: A defender's view inside a #DarkSide ransomware attack ***
What to expect when you’re targeted by a headline-seeking threat actor... (a thread)
1/8
What to expect when you’re targeted by a headline-seeking threat actor... (a thread)
1/8

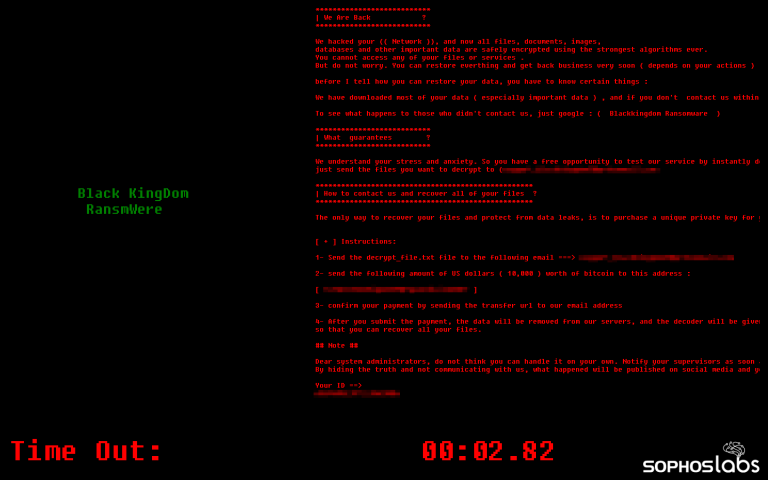
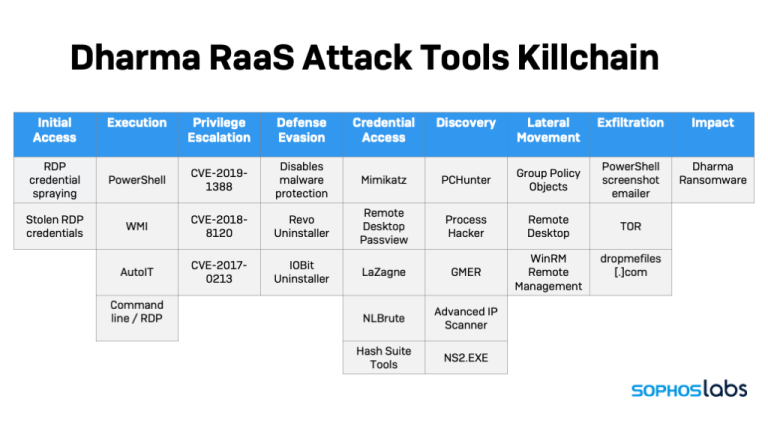
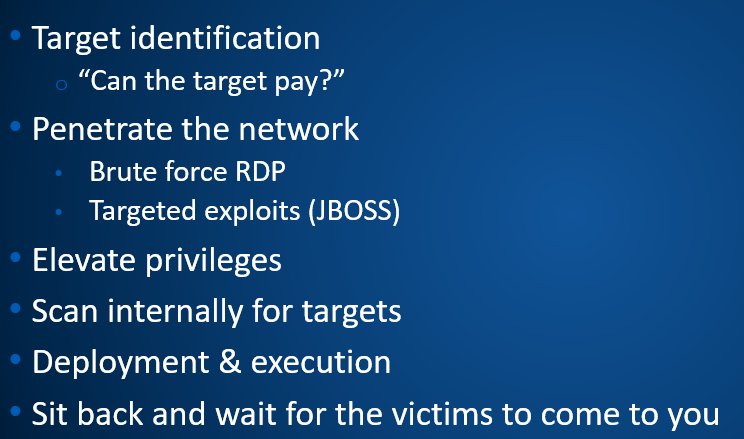
The recent ransomware intrusion of a major US gasoline pipeline operator was the work of an affiliate of #DarkSide, a ransomware ring that has been responsible for at least 60 known cases of ransomware double-extortion so far this year.
2/8
2/8
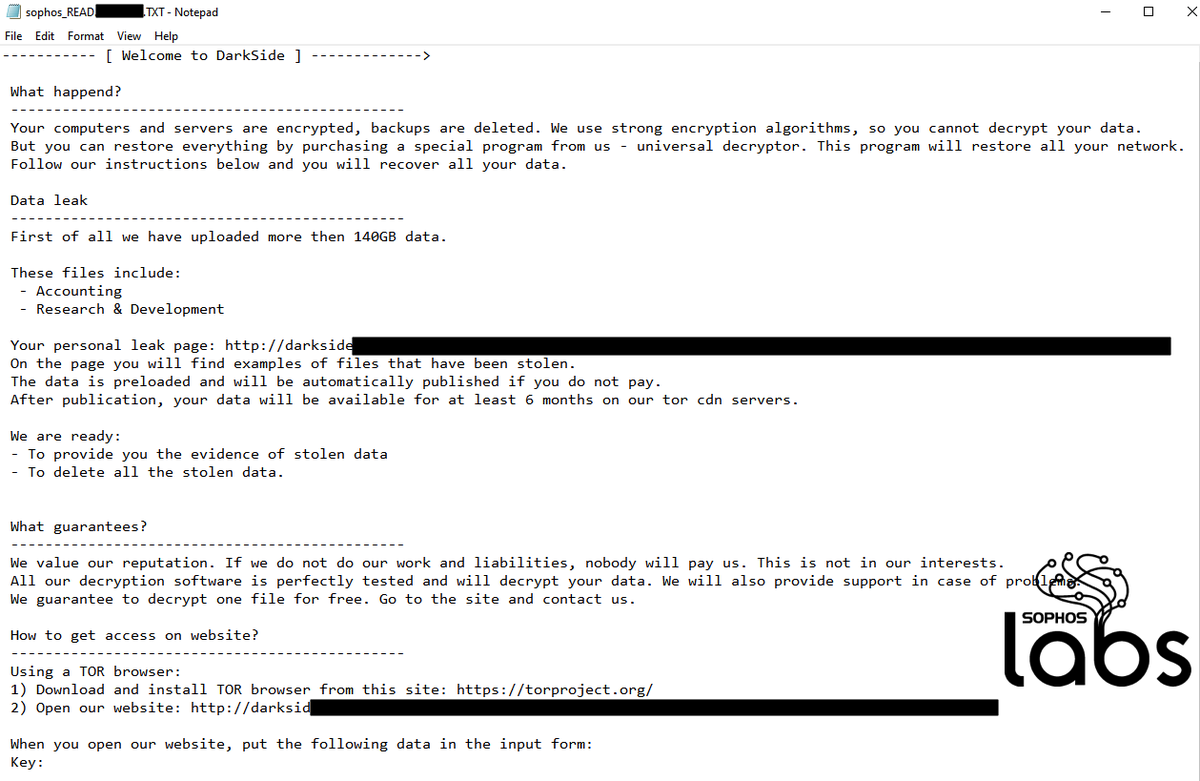
DarkSide has struck several high-profile victims recently, including companies listed on the NASDAQ stock exchange.
3/8
3/8
But the disruption of Colonial Pipeline's network led to the company shutting down its operational technology (OT) network as well—effectively cutting off a majority of the gasoline supply to the eastern United States.
4/8
4/8
The shutdown of #ColonialPipeline is not the first critical infrastructure issue triggered by a ransomware attack. Last February, a US-based natural gas facility was shut down for two days by a ransomware intrusion that spread to its OT network.
5/8
5/8
And DarkSide has not avoided these types of companies, either, hitting a Brazilian energy company earlier this year. But the Colonial incident has potentially greater real-world impact—and has apparently made DarkSide’s operators more notorious than they’re comfortable with.
6/8
6/8
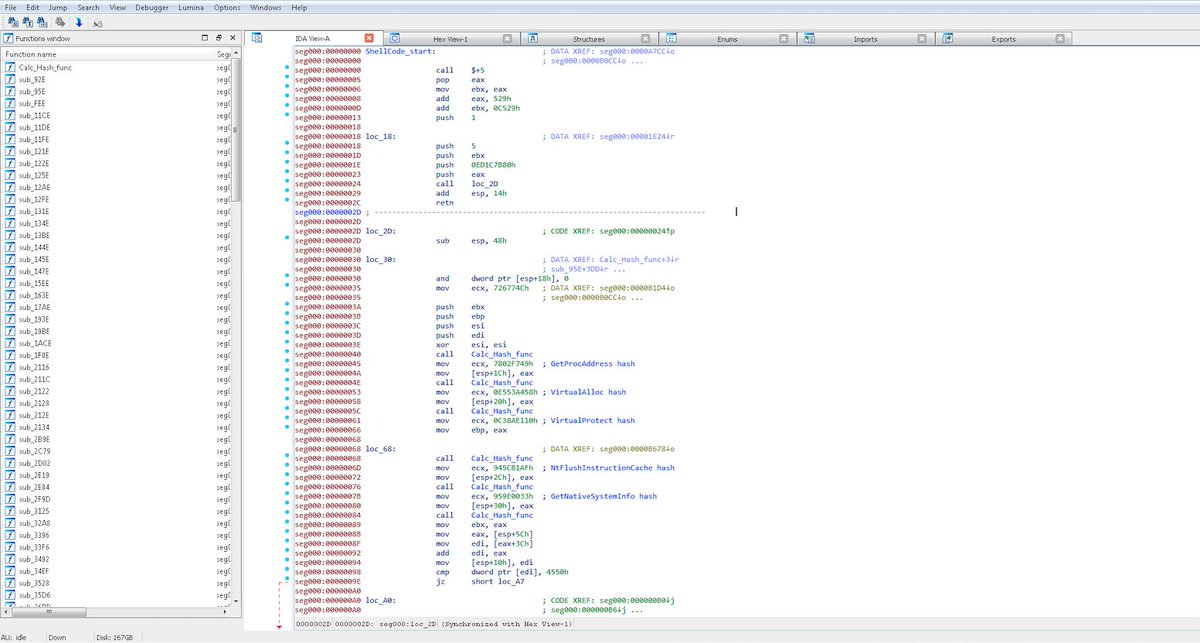
The Sophos Rapid Response team has been called in for incident response or to intervene during an attack involving DarkSide on at least five different instances in the past year.
7/8
7/8

See our full #DarkSide report: news.sophos.com/en-us/2021/05/…
By @thepacketrat @markloman @AltShiftPrtScn
SophosLabs would like to acknowledge Yusuf Arslan Polat, Gabor Szappanos, Suriya Natarajan, Szabolcs Lévai, and Ferenc László Nagy for their contributions to this post.
8/8


By @thepacketrat @markloman @AltShiftPrtScn
SophosLabs would like to acknowledge Yusuf Arslan Polat, Gabor Szappanos, Suriya Natarajan, Szabolcs Lévai, and Ferenc László Nagy for their contributions to this post.
8/8



• • •
Missing some Tweet in this thread? You can try to
force a refresh