NEW on Patch Tuesday: Six in-the-wild exploits patched in Microsoft’s June security fix release
Security fixes address five critical vulnerabilities, including scripting and Defender bugs—and one actively exploited flaw in MSHTML...
(a thread) 1/7
Security fixes address five critical vulnerabilities, including scripting and Defender bugs—and one actively exploited flaw in MSHTML...
(a thread) 1/7
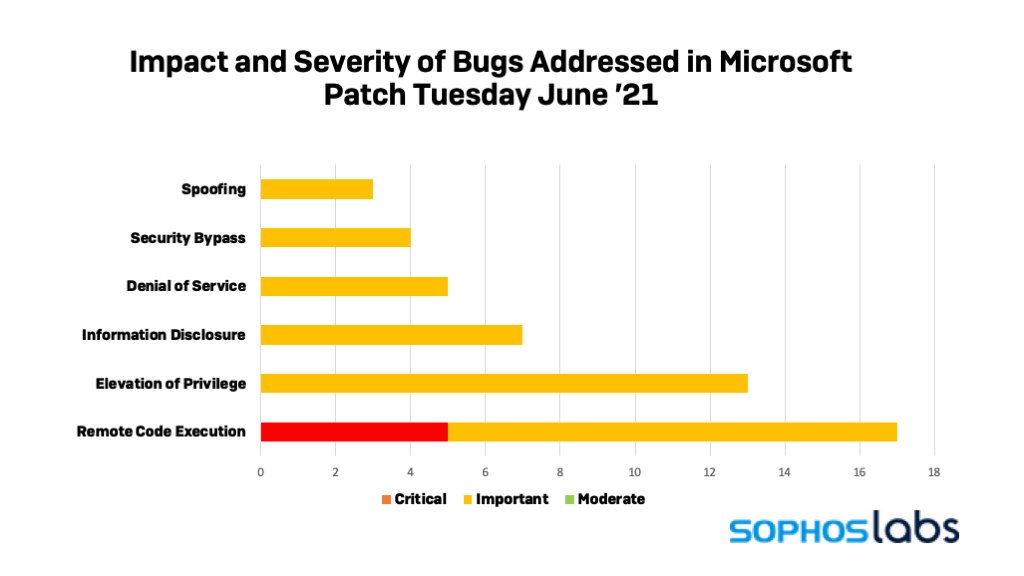
The June security update drop has a mere 49 new vulnerability fixes, plus five synchronized fixes delivered by Adobe.
Only five of Microsoft’s bug fixes are rated as critical. But that doesn’t lessen the importance of applying patches as soon as possible. 2/7
Only five of Microsoft’s bug fixes are rated as critical. But that doesn’t lessen the importance of applying patches as soon as possible. 2/7
All five critical patches are for bugs that are potentially exploitable for remote code execution (RCE). And one of them, a vulnerability in the Windows MSHTML “platform”, is already being exploited. 3/7
Microsoft also pushed a fix for an elevation of privilege vulnerability in the Chromium-based Microsoft Edge browser (CVE-2021-33741) on June 4.
That vulnerability, also reported in Chrome, was already being actively exploited in the wild. 4/7
That vulnerability, also reported in Chrome, was already being actively exploited in the wild. 4/7
Sophos protection:
Here is a list of protection released by SophosLabs in response to this advisory to complement any existing protection and generic exploit mitigation capabilities in our products. 6/7
Here is a list of protection released by SophosLabs in response to this advisory to complement any existing protection and generic exploit mitigation capabilities in our products. 6/7

• • •
Missing some Tweet in this thread? You can try to
force a refresh