#ESETresearch has recently discovered a new undocumented modular backdoor, SideWalk, that was used by an APT group we named SparklingGoblin during one of its recent campaigns targeting a US-based computer retail company 🇺🇸. welivesecurity.com/2021/08/24/sid… @passil_t @mathieutartare 1/6
SideWalk is a modular backdoor that can dynamically load additional modules sent from the C&C server, makes use of Google Docs as a dead drop resolver, and @Cloudflare workers as a C&C server. It can also properly handle communication behind a proxy. 2/6
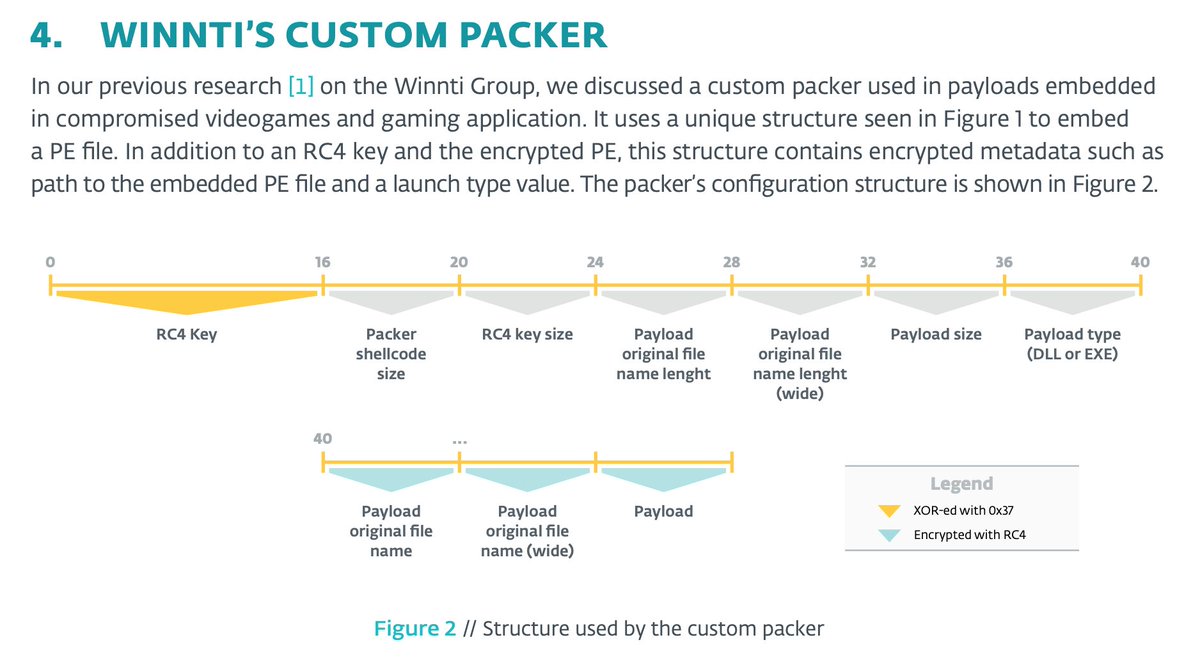
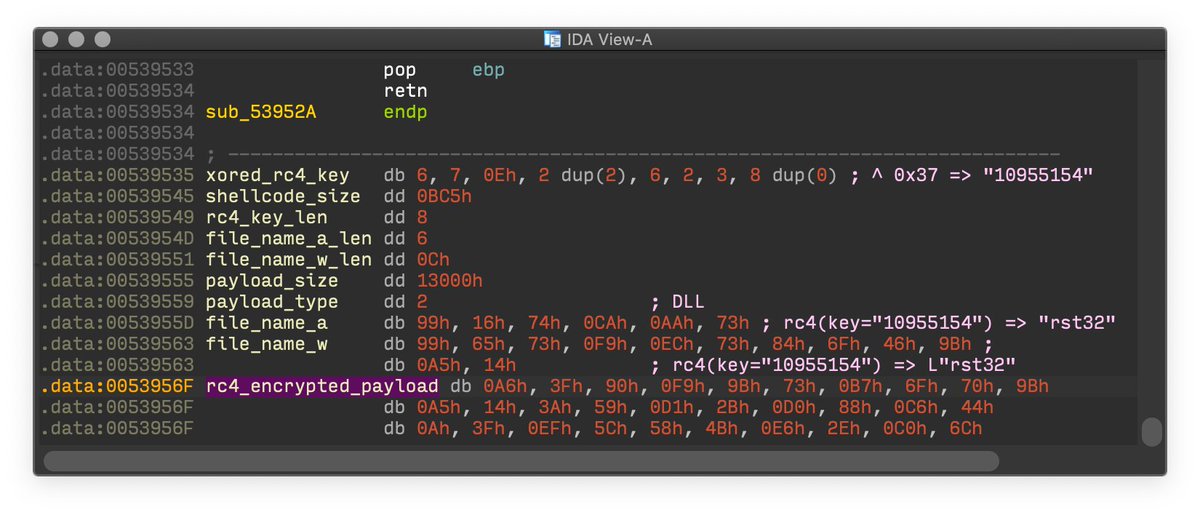
This backdoor shares multiple similarities with another backdoor used by the group: CROSSWALK, which FireEye was first to attribute to #APT41. This backdoor is referenced as ScrambleCross by Trend Micro 3/6
SparklingGoblin is a group with some level of connection to #Winnti Group. It was very active in 2020 and the first half of 2021, compromising multiple organizations over a wide range of verticals around the world with a particular focus on the academic sector and East Asia. 4/6
Today’s @TrendMicroRSRCH publication about Earth Baku’s campaign using the ScrambleCross backdoor corresponds to what we track as the SparklingGoblin group and the SideWalk backdoor. trendmicro.com/en_ph/research…. 5/6
The content of our blog post was published in June as part of our ongoing coverage of SparklingGoblin in #ESETresearch private report feed. 6/6
• • •
Missing some Tweet in this thread? You can try to
force a refresh