How Kubernetes differs from Docker in the way it deals with containers 🔽
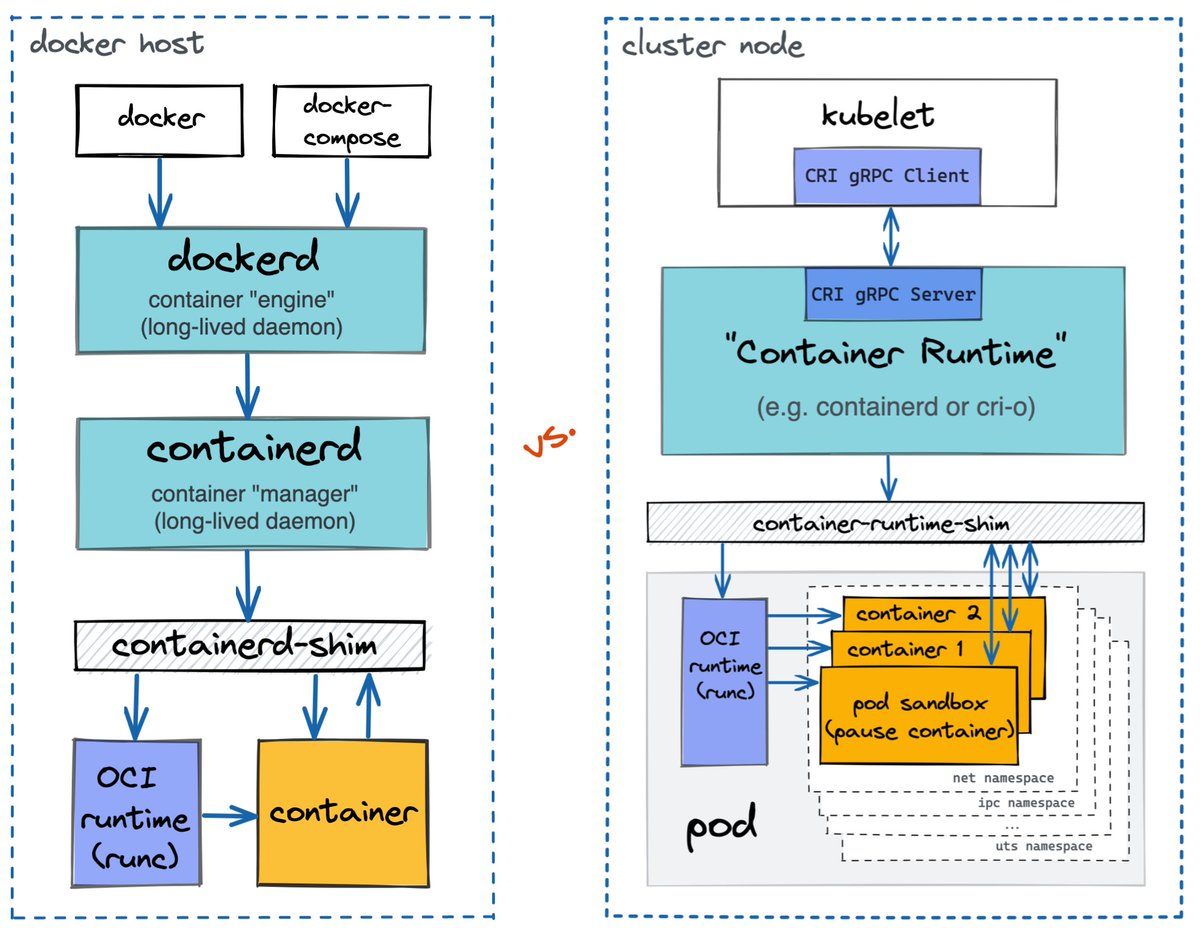
Under the hood, Kubernetes and Docker both rely on the same/similar lower-level components to run containers.
Often, both use containerd and runc. However, Kubernetes makes the container runtime pluggable
Under the hood, Kubernetes and Docker both rely on the same/similar lower-level components to run containers.
Often, both use containerd and runc. However, Kubernetes makes the container runtime pluggable
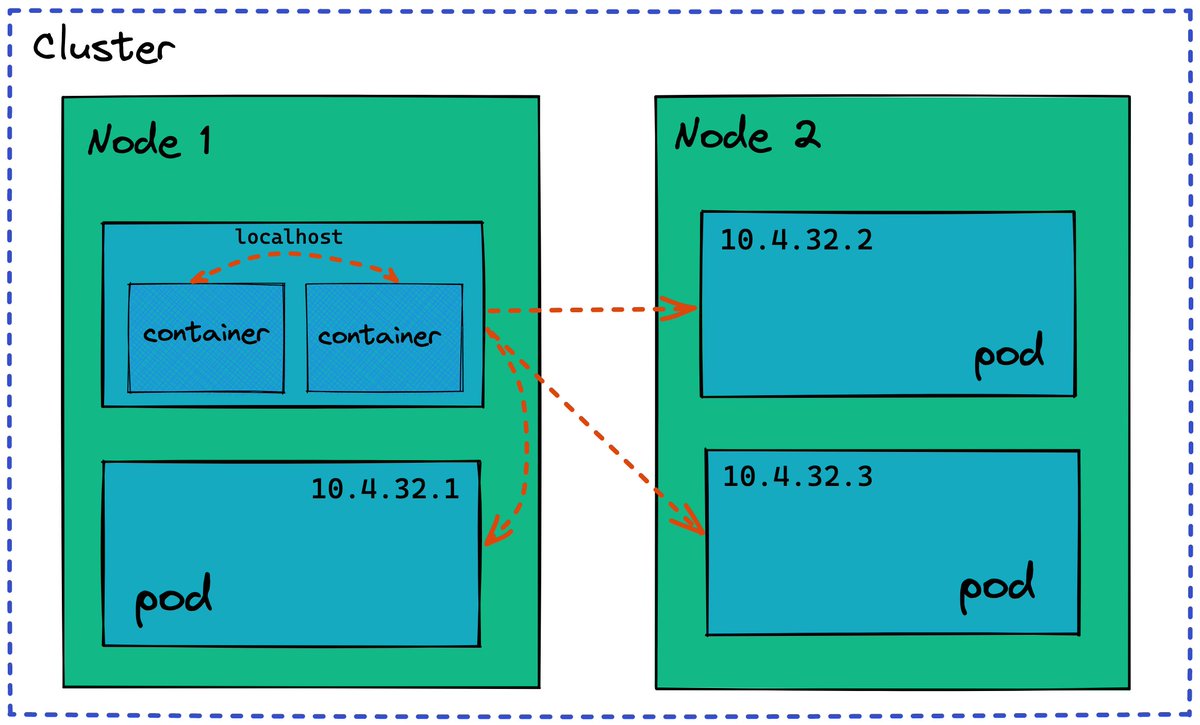
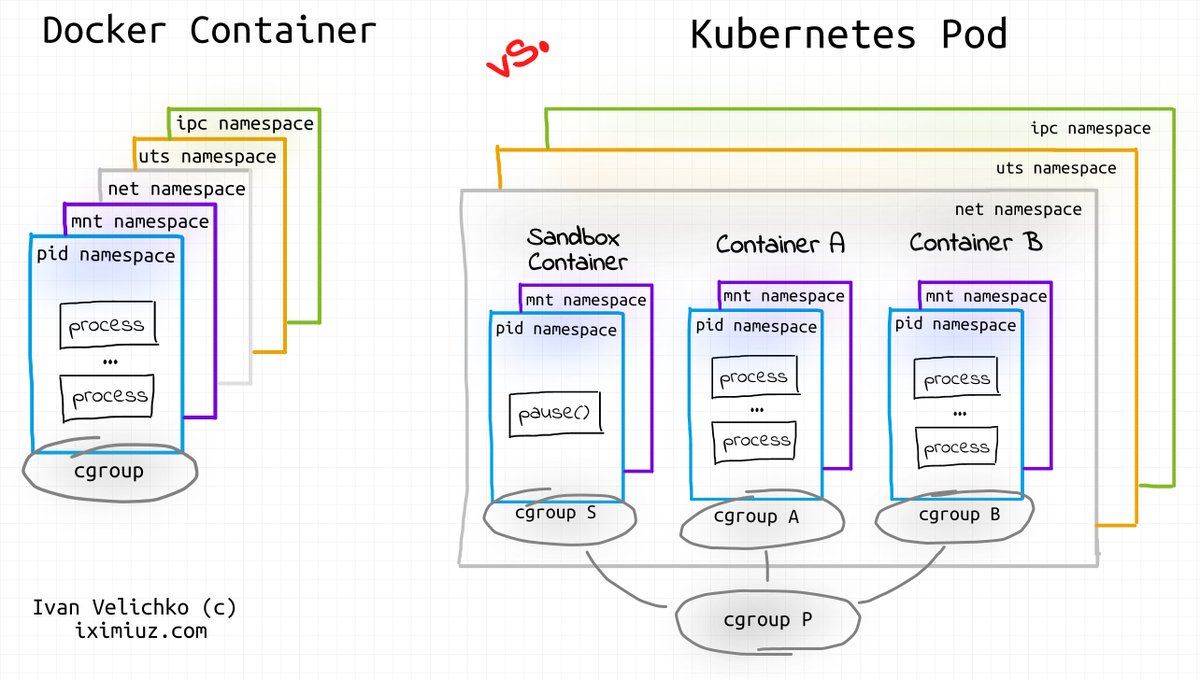
Even when Kubernetes uses exactly the same container runtime as Docker, the implementation of Pods differs from the implementation of Containers.
Pods are more than just groups of containers. Containers in a pod share net, ipc, and uts namespaces making pods more similar to VMs.
Pods are more than just groups of containers. Containers in a pod share net, ipc, and uts namespaces making pods more similar to VMs.
Not all Containers are Linux containers!
OCI Runtime Spec doesn't limit container implementation to namespaces and cgroups. And VM-based containers is a real thing!
Some of the container runtimes supported by Kubernetes (e.g., Kata), launch a micro-VM per Pod.
OCI Runtime Spec doesn't limit container implementation to namespaces and cgroups. And VM-based containers is a real thing!
Some of the container runtimes supported by Kubernetes (e.g., Kata), launch a micro-VM per Pod.

Check out an in-depth analysis of how Pods differ from Containers from the implementation standpoint:
iximiuz.com/en/posts/conta…
iximiuz.com/en/posts/conta…
Learn why and how to use containerd - one of the most widely used container runtimes - without Docker or Kubernetes:
iximiuz.com/en/posts/conta…
iximiuz.com/en/posts/conta…
• • •
Missing some Tweet in this thread? You can try to
force a refresh