NEW ransomware actor uses password-protected archives to bypass encryption protection
Calling themselves "Memento team", actors use Python-based ransomware that they reconfigured after setbacks...
1/13
Calling themselves "Memento team", actors use Python-based ransomware that they reconfigured after setbacks...
1/13

In late October, Sophos MTR’s Rapid Response Team encountered a new ransomware group with an interesting approach to holding victims’ files hostage.
The ransomware used by this group, who identify themselves as “Memento Team,” doesn’t encrypt files. 2/13
The ransomware used by this group, who identify themselves as “Memento Team,” doesn’t encrypt files. 2/13
Instead, it copies files into password-protected archives, using a renamed freeware version of the legitimate file utility WinRAR—and then encrypts the password and deletes the original files. 3/13 

This was a retooling by the ransomware actors, who initially attempted to encrypt files directly—but were stopped by endpoint protection. After failing on the first attempt, they changed tactics, and re-deployed, as evidenced by the multiple versions of... 4/13
... the ransomware payload compiled at different times found on the victim’s network.
They then demanded $1 million US to restore the files, and threatened data exposure if the victim did not comply.
There were some other twists to the “Memento” attack as well. 5/13
They then demanded $1 million US to restore the files, and threatened data exposure if the victim did not comply.
There were some other twists to the “Memento” attack as well. 5/13
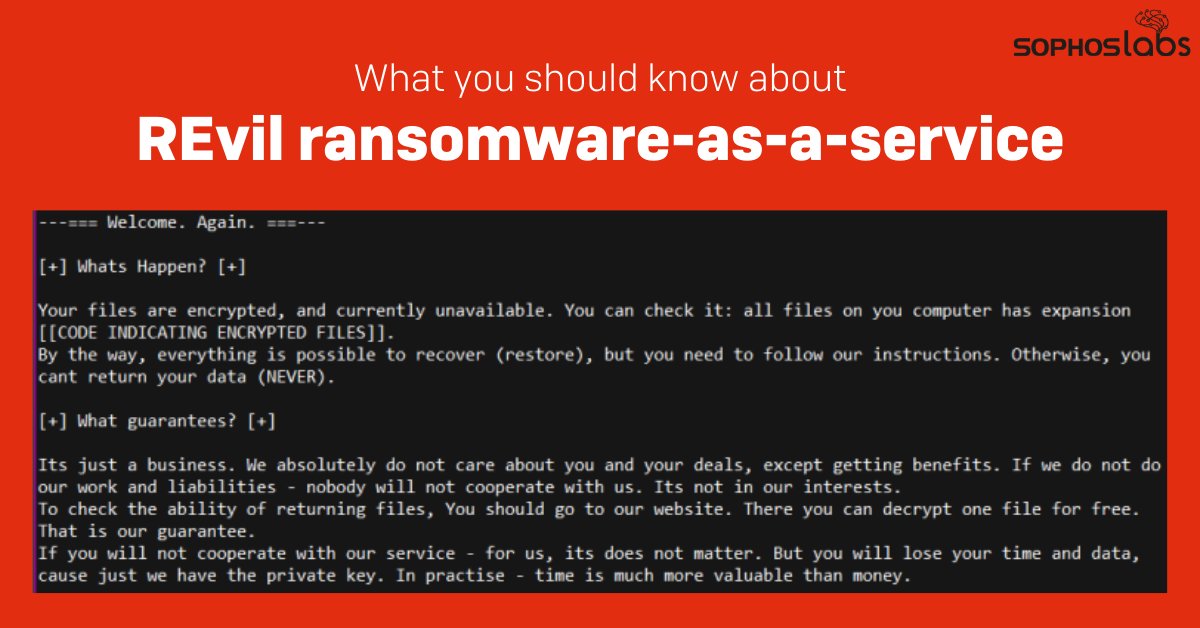
The ransomware itself is a Python 3.9 script compiled with PyInstaller. And in a ransom note that largely cribs the format used by REvil, the criminals behind the ransomware instructed the victims to contact them via a Telegram account. 6/13 

The attackers also deployed an open-source Python-based keylogger on several machines as they moved laterally within the network using Remote Desktop Protocol. 7/13
The Memento actors also waited a long time before executing their attack—so long that at least two different cryptocurrency miners were dropped onto the server they used for initial access during the course of their dwell time by different intruders using similar exploits. 8/13
After over 6 months dwell time on the victim’s network, the attack had finally been sprung.
Unfortunately for the Memento actors, all that extra work did not pay off as planned. The victim did not negotiate with the ransomware actors. 9/13
Unfortunately for the Memento actors, all that extra work did not pay off as planned. The victim did not negotiate with the ransomware actors. 9/13
Thanks to backups, the targeted organization was able to restore most of their data. For systems running InterceptX, the endpoint detection and response system logged the commands used by the attack to archive files, along with the unencrypted passwords for the files. 10/13
SophosLabs and Sophos Rapid Response were able to recover select files for the victim and provide a method for recovering any files not backed up.
A list of the IOCs for the Memento attack and the miner attacks from this incident is available on SophosLabs’ GitHub page. 11/13
A list of the IOCs for the Memento attack and the miner attacks from this incident is available on SophosLabs’ GitHub page. 11/13
We'd like to thank Vikas Singh, Robert Weiland, Elida Leite, Kyle Link, Ratul Ghosh, Harinder Bhathal, and Sergio Bestuilic of Sophos MTR’s Rapid Response team, and Ferenc László Nagy, Rahul Dugar, Nirav Parekh, and Gabor Szappanos of SophosLabs for their contributions. 13/13
• • •
Missing some Tweet in this thread? You can try to
force a refresh