NEW: Conti affiliates use ProxyShell Exchange exploit in ransomware attacks ⚠️
In one of the ProxyShell-based attacks observed by Sophos, the Conti affiliates managed to gain access to the target’s network and set up a remote web shell in under a minute...
1/14
In one of the ProxyShell-based attacks observed by Sophos, the Conti affiliates managed to gain access to the target’s network and set up a remote web shell in under a minute...
1/14
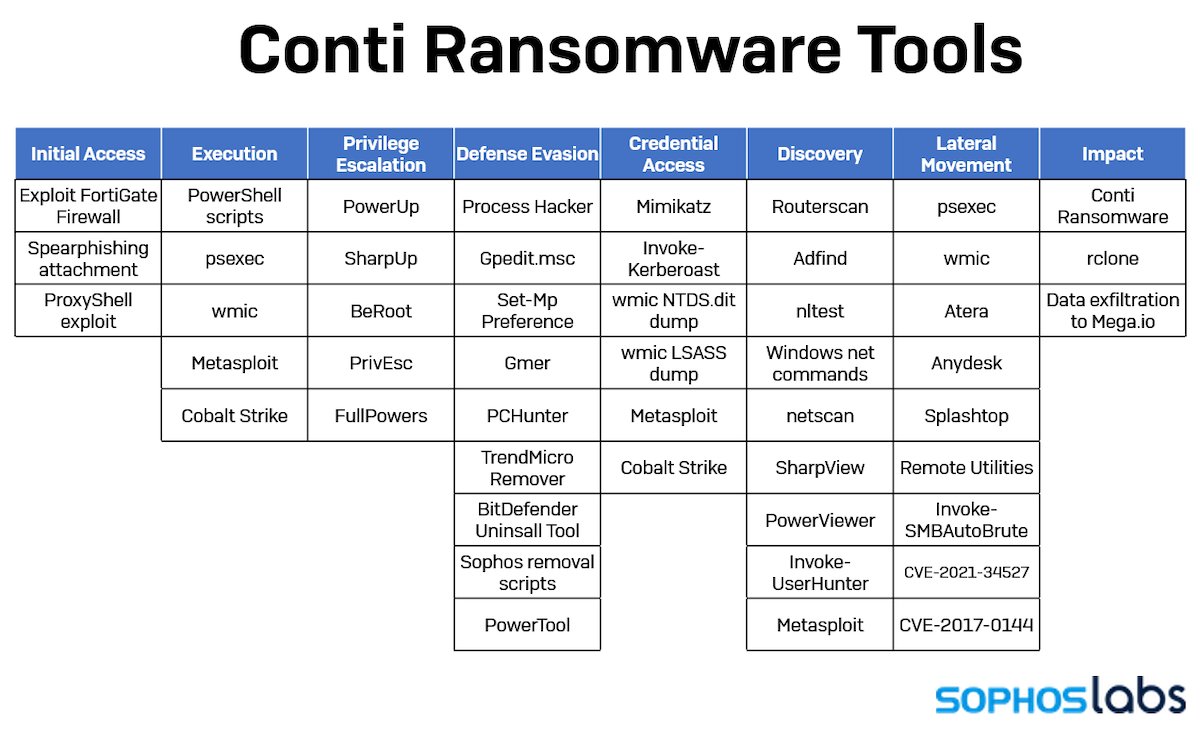
ProxyShell represents an evolution of the ProxyLogon attack method. In recent months, the exploit has become a mainstay of ransomware attacker playbooks, including those deploying the new LockFile ransomware first seen in July. 2/14 

As attackers have gained experience with the techniques, their dwell time before launching the final ransomware payload on target networks has decreased from weeks to days to hours. 3/14
1 MINUTE
In the case of one of the group of ProxyShell-based attacks observed by Sophos, the Conti affiliates managed to gain access to the target’s network and set up a remote web shell in under a minute. 4/14
In the case of one of the group of ProxyShell-based attacks observed by Sophos, the Conti affiliates managed to gain access to the target’s network and set up a remote web shell in under a minute. 4/14
3 MINUTES
Three minutes later, they installed a second, backup web shell. 5/14
Three minutes later, they installed a second, backup web shell. 5/14
30 MINUTES
Within 30 minutes they had generated a complete list of the network’s computers, domain controllers, and domain administrators. 6/14
Within 30 minutes they had generated a complete list of the network’s computers, domain controllers, and domain administrators. 6/14
FOUR HOURS
Just four hours later, the Conti affiliates had obtained the credentials of domain administrator accounts and began executing commands. 7/14
Just four hours later, the Conti affiliates had obtained the credentials of domain administrator accounts and began executing commands. 7/14
48 HOURS
Within 48 hours of gaining that initial access, the attackers had exfiltrated about 1 Terabyte of data. 8/14
Within 48 hours of gaining that initial access, the attackers had exfiltrated about 1 Terabyte of data. 8/14
5 DAYS
After five days had passed, they deployed the Conti ransomware to every machine on the network, specifically targeting individual network shares on each computer. 9/14
After five days had passed, they deployed the Conti ransomware to every machine on the network, specifically targeting individual network shares on each computer. 9/14
Over the course of the intrusion, the Conti affiliates installed no fewer than seven back doors on the network: two web shells, Cobalt Strike, and four commercial remote access tools (AnyDesk, Atera, Splashtop and Remote Utilities). 10/14
The web shells, installed early on, were used mainly for initial access; Cobalt Strike and AnyDesk were the primary tools they used for the remainder of the attack. 11/14
IOCs
The encoded PowerShell commands from this attack are provided in the article linked below for threat researchers and responders. 12/14
The encoded PowerShell commands from this attack are provided in the article linked below for threat researchers and responders. 12/14
See all the technical details from @thepacketrat and @AltShiftPrtScn: news.sophos.com/en-us/2021/09/…
13/14
13/14
SophosLabs would like to acknowledge Anand Ajjan, Andrew Ludgate, and Gabor Szappanos of SophosLabs, and Sergio Bestulic and Syed Zaidi from Sophos MTR’s Rapid Response Team for their contributions to this report. 14/14
• • •
Missing some Tweet in this thread? You can try to
force a refresh