[#thread 🧵] Last week in #Microsoft #PatchTuesday, a critical vulnerability was patched that theoretically allows attackers to achieve Remote Code Execution on a target #IIS server (CVE-2022-21907). I'll explain how it works in this thread ⬇️ 
[#thread 🧵(2/9)] A bit of History !
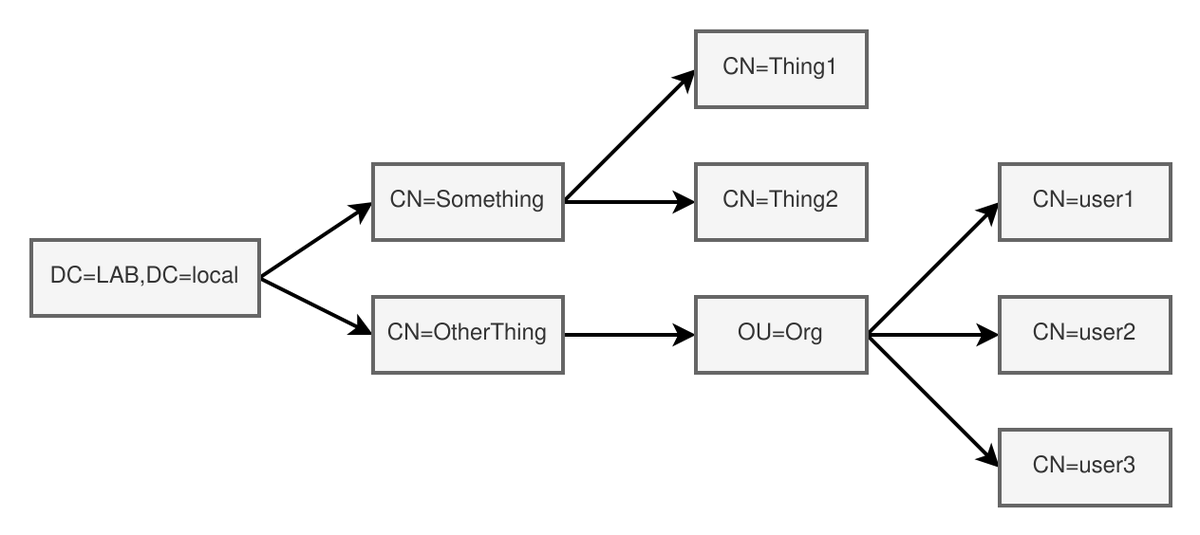
First of all, it is important to know that this vulnerability is a sibling of CVE-2021-31166 disclosed in May of last year. These two vulnerabilities occur in the parsing of HTTP headers of an incoming request, within the http.sys driver.
First of all, it is important to know that this vulnerability is a sibling of CVE-2021-31166 disclosed in May of last year. These two vulnerabilities occur in the parsing of HTTP headers of an incoming request, within the http.sys driver.

[#thread 🧵(3/9)] But what happens exactly 🤔 ?
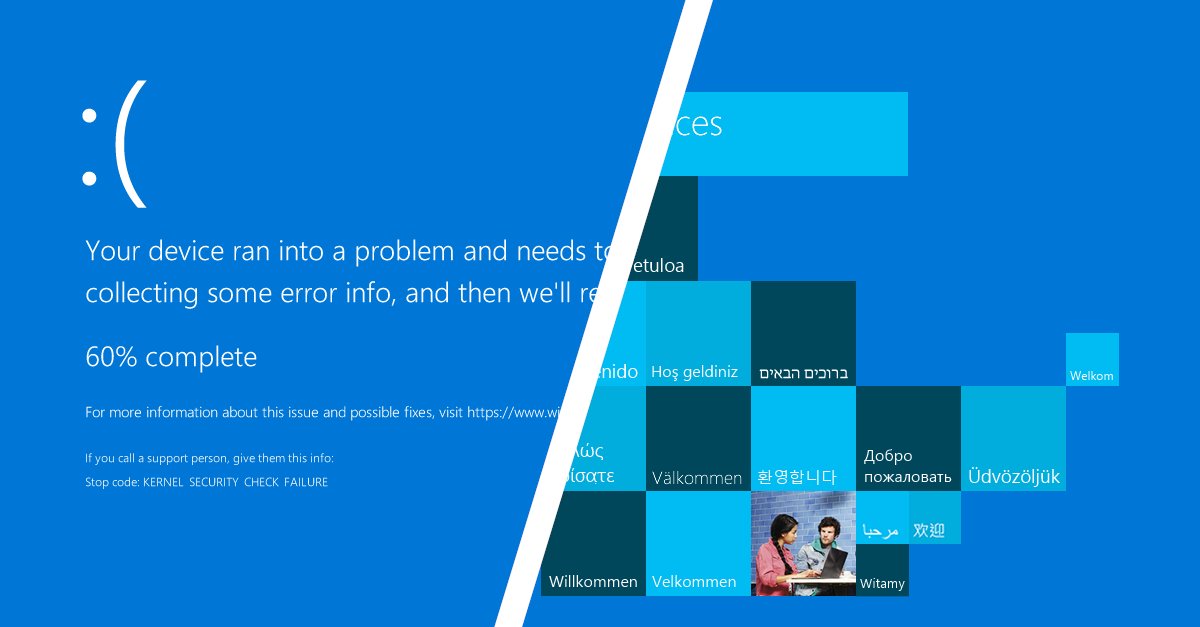
To understand what happens in a kernel driver crash, It's important to analyze the kernel #crashdump generated at the moment of the blue screen! Let's open it in #WinDbg and analyze it!
To understand what happens in a kernel driver crash, It's important to analyze the kernel #crashdump generated at the moment of the blue screen! Let's open it in #WinDbg and analyze it!

[#thread 🧵(4/9)] WinDbg analysis 🔍
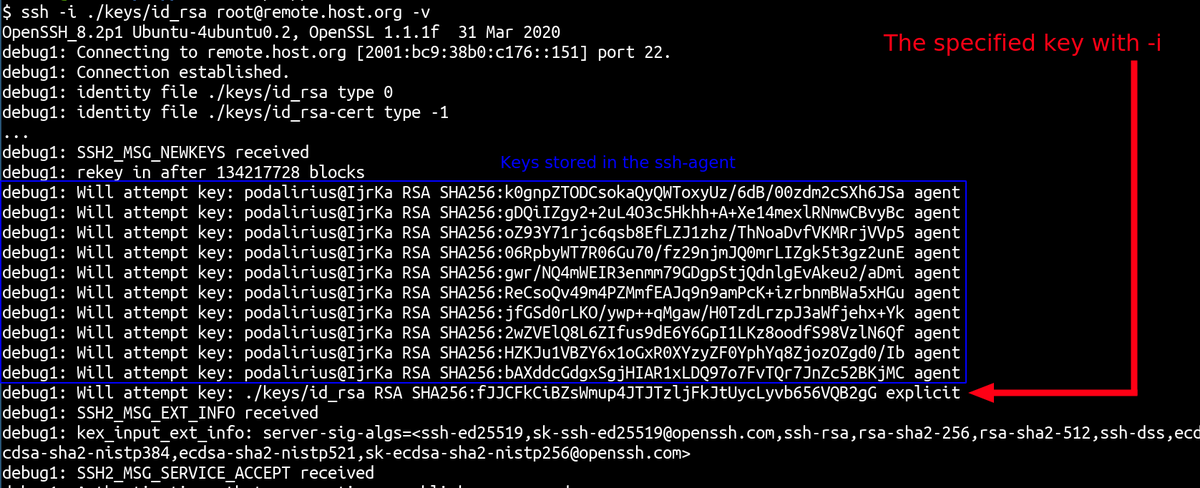
With a quick analysis, WinDbg detects that a corrupted list triggered the crash in UlFreeUnknownCodingList. We also have all the function call graph at the moment of the crash, as well as registers values!
With a quick analysis, WinDbg detects that a corrupted list triggered the crash in UlFreeUnknownCodingList. We also have all the function call graph at the moment of the crash, as well as registers values!

[#thread 🧵(5/9)] Functions call graph 📈
When an invalid Accept-Encoding is passed to #UlpParseAcceptEncoding function, it processes it and gives it to #UlFreeUnknownCodingList. The invalid content-codings of a circular doubly linked list are then freed and the driver crashes.
When an invalid Accept-Encoding is passed to #UlpParseAcceptEncoding function, it processes it and gives it to #UlFreeUnknownCodingList. The invalid content-codings of a circular doubly linked list are then freed and the driver crashes.

[#thread 🧵(6/9)] So where is my RCE ? 🥺
Unfortunately, its only theoretical to achieve RCE with this vulnerability. Given what we can control in the crash there is not much things we can do besides crashing a remote server for now.
Unfortunately, its only theoretical to achieve RCE with this vulnerability. Given what we can control in the crash there is not much things we can do besides crashing a remote server for now.
[#thread 🧵(7/9)] Video proof of concept 📺
Here is a video PoC of the crash on a Windows 10 2004 (The source code used is in the next tweet):
Here is a video PoC of the crash on a Windows 10 2004 (The source code used is in the next tweet):
[#thread 🧵(8/9)] Proof of concept code 🧑💻
The proof of concept code of the crash for CVE-2022-21907 can be found here:
github.com/p0dalirius/CVE…
The proof of concept code of the crash for CVE-2022-21907 can be found here:
github.com/p0dalirius/CVE…
[#thread 🧵(9/9)] I hope you liked this thread! I definitely had some fun reversing the #PatchTuesday last week 😍🥳
[#thread 🧵(10/10)] Additional references
This writeup from @thezdi about the CVE from last year is really good and helps understanding how http.sys works: zerodayinitiative.com/blog/2021/5/17…
This writeup from @thezdi about the CVE from last year is really good and helps understanding how http.sys works: zerodayinitiative.com/blog/2021/5/17…
• • •
Missing some Tweet in this thread? You can try to
force a refresh