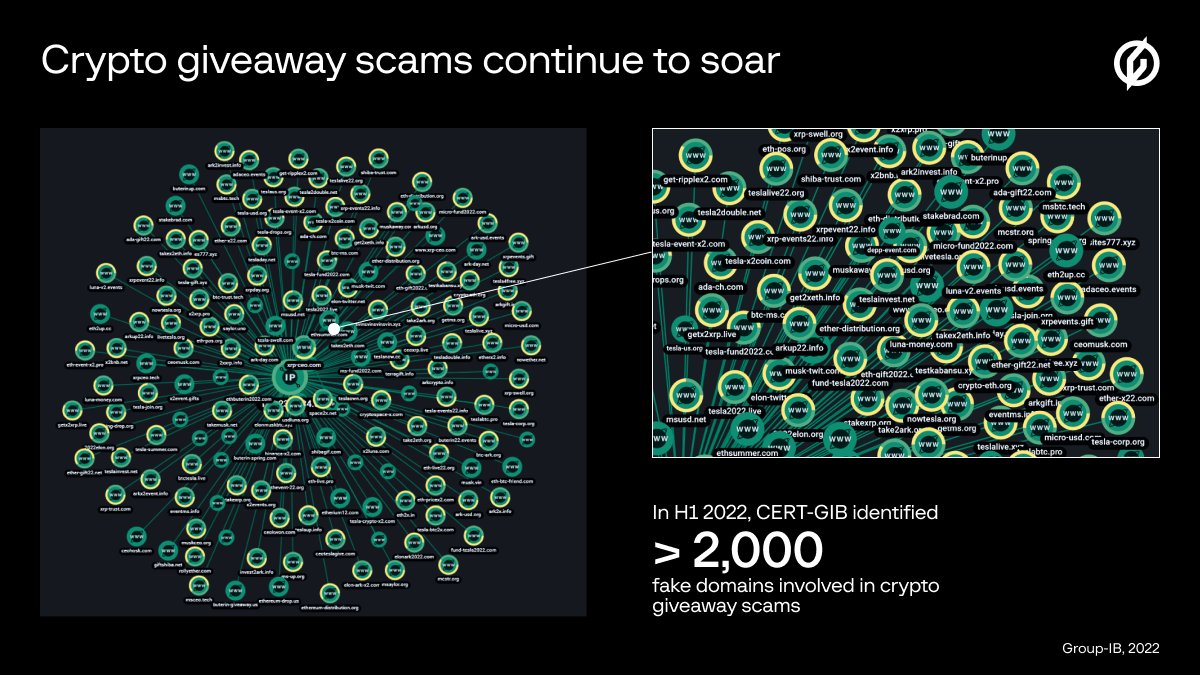
Crypto giveaway scams continue to soar: Group-IB has noted a fivefold increase in the number of domains used for #crypto giveaway #scams that involve fake #YouTube streams in the first half of 2022: bit.ly/3eWN0eL
#CryptoGiveaway
#CryptoGiveaway

According to Group-IB, 63% of the new fraudulent domain names were registered with Russian registrars, but the #fake websites are primarily designed to target English and Spanish-speaking #crypto investors in the US and other countries: bit.ly/3eWN0eL 

In the first six months of 2022, @CERTGIB identified more than 2,000 domains registered explicitly to be used as #fake promotion websites. This figure increased almost five-fold compared to the second half of 2021 and 53-fold in comparison with H1 2021: bit.ly/3eWN0eL 
#Scammers keep up with the latest headlines. One of the names most recently used as bait was Nayib Bukele, 43rd president of El Salvador. In 2021 El Salvador became the first country to adopt #bitcoin as the national currency:
bit.ly/3eWN0eL
bit.ly/3eWN0eL

The phenomenal growth of fake #crypto giveaways can be explained by a significantly enhanced arsenal and availability of tools for crypto #scammers, even with low technical skills. Want to learn more? Check out our website➡️ bit.ly/3eWN0eL 

• • •
Missing some Tweet in this thread? You can try to
force a refresh