- Nate Cardozo, @EFF
- where do you keep the secret list of those to be spied upon?
- how do you deal with app-reinstalls deleting surveillance enablement?
- how do you hide from app-forensics?
To be effective the following will need to be written on the outside of most, possibly _every_ message "envelope" that they receive:
- snake oil
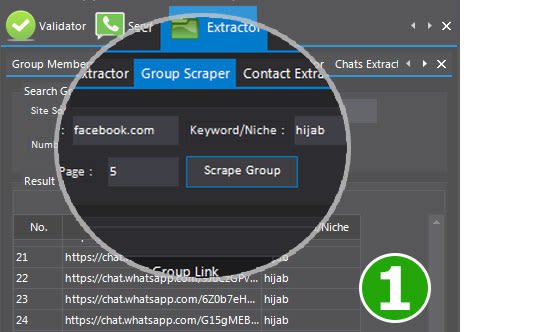
- vectors for malware & ad-injection
- causes of crashes (see #11, above)
- exfiltration of "secure" E2E messages, at-scale
- bad user experiences
…and will need to be combatted by the (eg) WhatsApp, or other messenger dev teams.
So: the Gov't will be inviting users to undermine their own security, by inviting users to break the application trust model / lard their phones with malware.
- leaking lists of the surveilled into the public domain
- and fomenting an ecosystem of malware
- driving people to use unsurveilled software
- and driving the bad guys away from platforms where at least there is comms metadata available.
- forcing platform providers like Facebook to implement surveillance-enabled software architectures, in a pursuit that is ultimately self-sabotaging and harmful to all parties, including law enforcement.
There's only one reasonable response to this:
blog.cryptographyengineering.com/2018/12/17/on-…
"For this surveillance mechanism to work, people will have to be prevented from [using helper apps to] access to data which exists on their own mobile devices, and we cannot achieve that."
❓