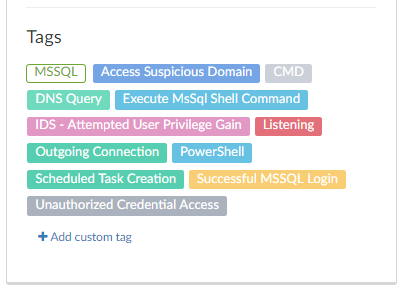
IOCs
instantrep.xyz
secured.com.awi-o.online
json.geoiplookup.io
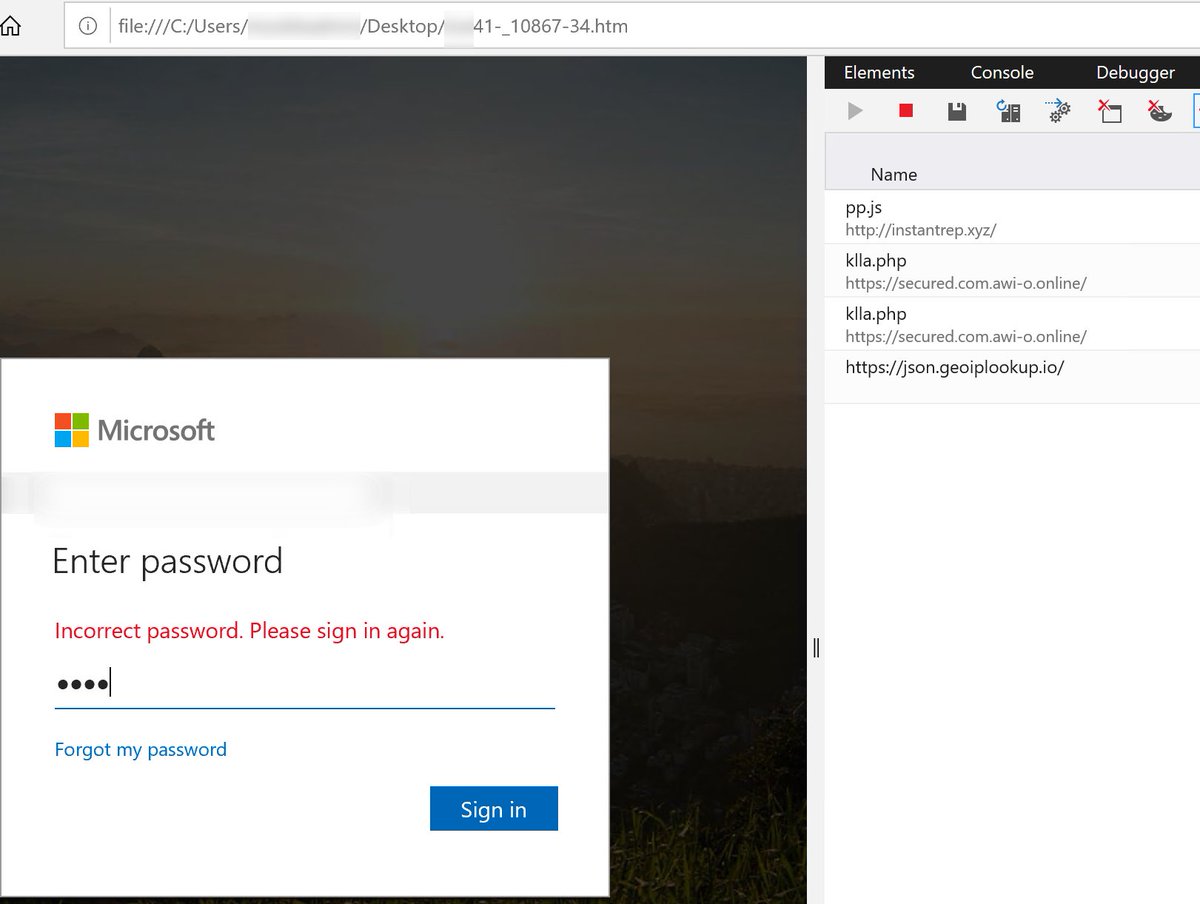
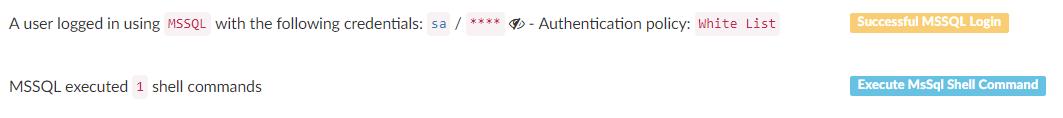
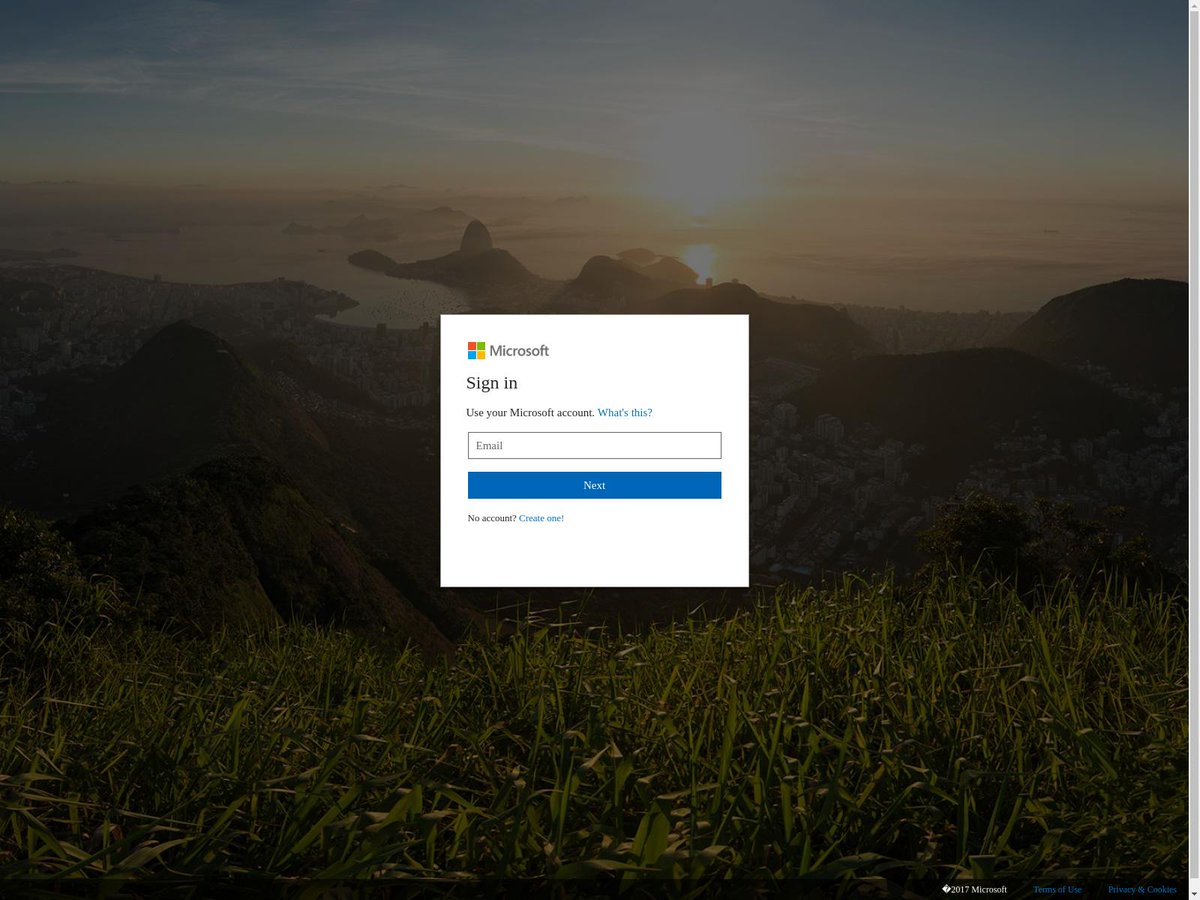
1. Originates from a compromised mailbox, so it passes SPF, DMARC and DKIM.
2. The .HTM is not malicious, so sandbox detonation is not a problem.
3. There is no remote URL attempted unless the user clicks their username.
"Remittance advice required."
Firstname Lastname (of compromised user)
CFO
Consider blocking .HTM attachments.