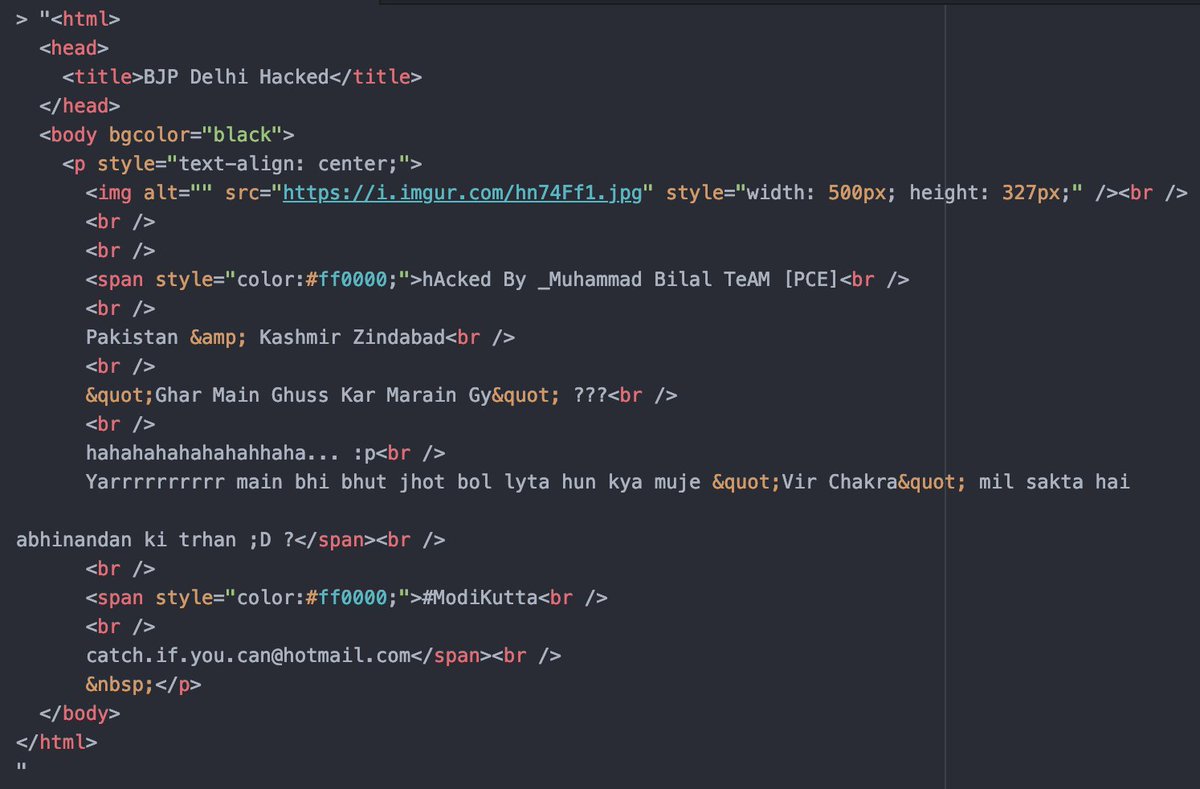
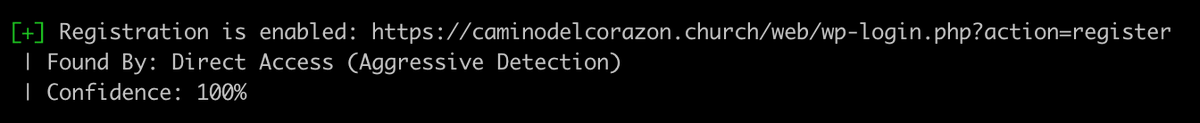
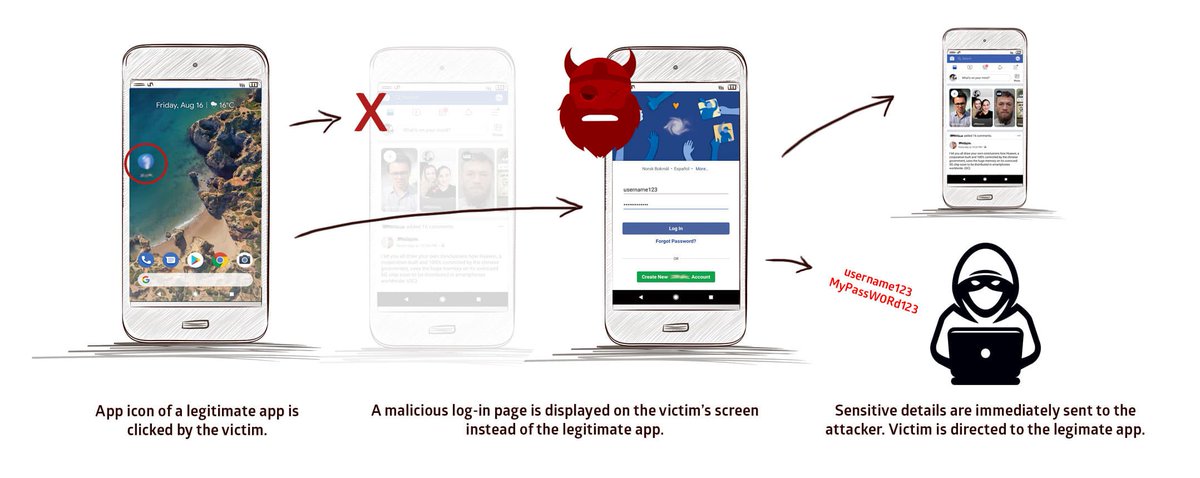
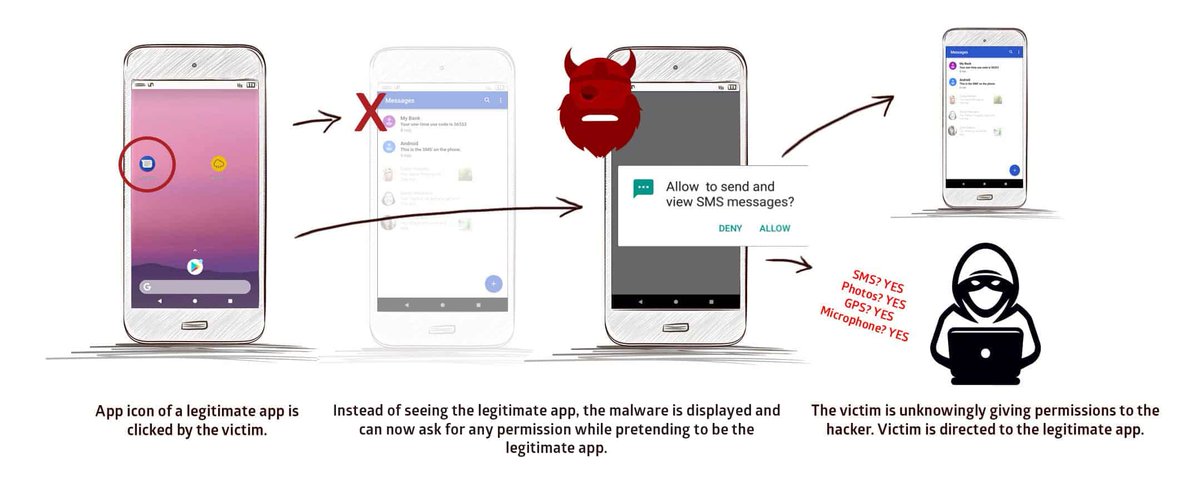
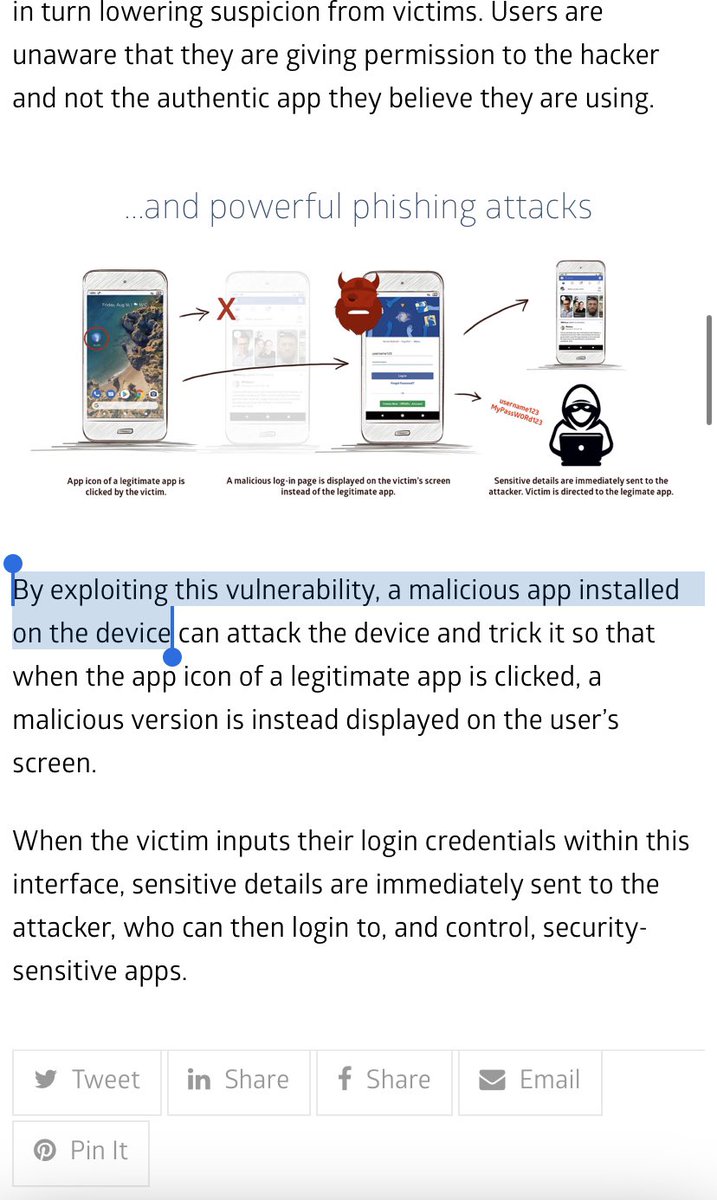
So a “new” #Android vulnerability with the usual pack (name, website, fancy logo) is in town. #StrandHogg is far from being new. Task hijacking in Android has been documented in 2015 usenix.org/system/files/c…
Plot twist: Nowhere, there don’t receive a number for it.