If you can open a device w/o the user noticing, you can also replace the hardware. And in particular, you can add a MITM *inside the device itself* between any secure element and the UI.
Defeating this kind of attack requires tamper protection of *all* the hardware, not just one chip.
W/ practice adding a MITM mod would take just a minute or two.
You'd be able to install Doom on it too if it were better HW.
The same person who did the sloppy Doom demo! But that's a 16yo kid, so I'll cut him slack; the rest of the team not so much.
It's a good thing that we can modify and inspect our devices, even hardware wallets! That's key to a healthy open source ecosystem, and real peer review of security.
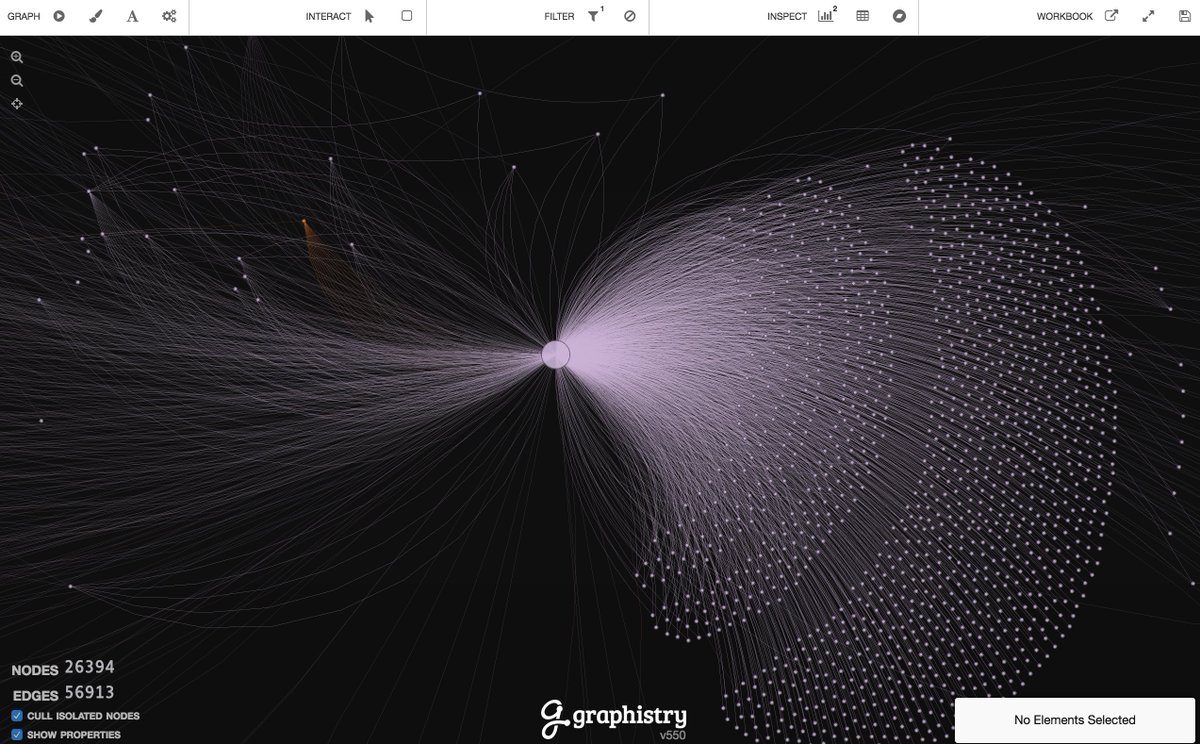
How many eyes are on the Trezor or Ledger source code vs Bitcoin Core?