TL;DR: Fusion ML💗Partner Datasets
In this release, we extend Fusion to partner ecosystem such as firewall Threat logs from Palo Alto Networks and our very own, MDATP
microsoft.com/security/blog/…
Deets⬇️1/
3/
We now extend this stitching together insights from Threat logs from @PaloAltoNtwks and Microsoft Defender ATP
4/
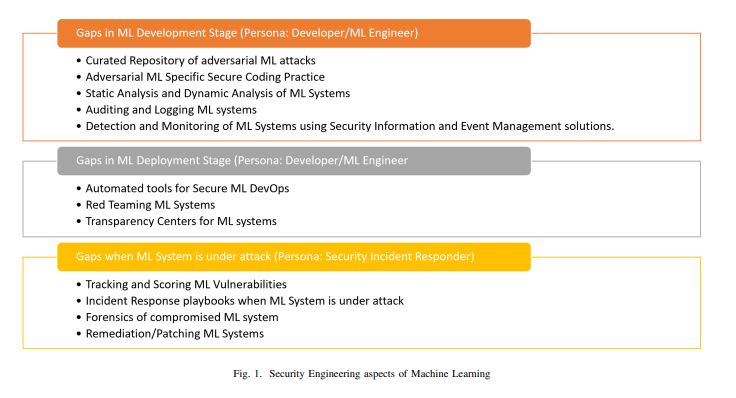
We had to overcome 2 problems for this release
Problem 1: Customers have many security products and are on many clouds. If we build a custom ML system for each of these datasets, we aint gonna scale.
Want: A flexible ML System that can accommodate new datasets
Want: A flexible system that can accomodate domain knowledge
7/
Want: An environment to test the system
8/
So one natural fit is using graphical methods. We had already invested in it in the previous release, so extending to other data sets.
9/
This was a double blind test:
- Ashwin did not know internals of detection logic
- ML team did not know anything about attack
Goal for ML team: Find Ashwin's shenanigans (We did!)
11/
1) the state of art ML techniques from the ML team
2) domain knowledge of MSTIC team from @ashwinpatil, @LeahLease and @JohnLaTwC
3) Good partnership with Partners @PaloAltoNtwks
4) Feedback from customers
12/
1) DM Me - Always open. Always want to hear from you
2) We will be at #RSAC2020 . Swing by and say hullo!